Defense contractors face a unique challenge when moving to the cloud: a single misconfigured storage bucket or unauthorized access by a foreign national can trigger ITAR violations with penalties reaching $1 million per incident. The stakes are high, but the path to compliance is clearer than many organizations realize.
This guide covers what makes cloud storage ITAR compliant, the specific technical requirements you’ll need to meet, and how to evaluate platforms and partners that can support your defense work.

ITAR compliant cloud storage ensures defense-related technical data is stored, processed, and accessed only by U.S. persons within U.S. borders. This type of storage features strict access controls, encryption, and comprehensive audit logs designed to meet the International Traffic in Arms Regulations—a U.S. regulatory framework that controls the export of defense articles and services.
Here’s the key concept: cloud storage becomes “ITAR compliant” when it prevents what the government considers an export of controlled data. Even storing data on a server that a foreign national could theoretically access counts as an export under ITAR.

For companies working in the defense supply chain, ITAR compliance isn’t optional—it’s a fundamental requirement for doing business. The consequences of getting it wrong extend far beyond regulatory fines, and the operational benefits of proper compliance make it worth the investment.
Defense contractors handling ITAR-controlled technical data are required to demonstrate strict compliance before winning or retaining government contracts. Prime contractors increasingly flow down ITAR requirements to their subcontractors as well. Without compliant infrastructure, you’re essentially locked out of the defense market entirely.
ITAR violations carry severe consequences that can threaten a company’s survival. Civil penalties can reach $1 million per violation, while criminal penalties include potential prison sentences. Perhaps more damaging, violations can result in debarment from future government contracts—effectively ending a company’s defense business.
Modern defense programs involve complex supply chains with multiple partners sharing technical data. ITAR compliant cloud storage provides a secure environment where authorized parties can collaborate without risking inadvertent export violations. This capability is particularly valuable when working with geographically distributed teams across the country.
Meeting ITAR requirements involves specific technical and administrative controls that go well beyond standard commercial cloud offerings. The table below summarizes the core requirements:
| Requirement | Description |
|---|---|
| Data Residency | All data physically stored on servers located within the United States |
| Access Control | Access strictly limited to verified U.S. persons only |
| Encryption | Data encrypted both in transit and at rest using validated methods |
| Audit Trails | Complete, immutable logs of all data access and administrative actions |
The foundation of ITAR compliance is keeping controlled data within U.S. borders and away from foreign persons. Your cloud provider’s data centers are located exclusively in the United States, but physical location alone isn’t enough—the people who administer those systems also matter.
Even employees of your own company who are foreign nationals cannot access ITAR data. This requirement extends to cloud provider staff, which is why specialized government cloud regions exist with personnel restrictions built in from the start.
ITAR requires robust encryption for data both at rest and in transit. The standard benchmark is FIPS 140-2 validated encryption modules, which have been tested and certified by the National Institute of Standards and Technology. FIPS 140-2 validation ensures the cryptographic methods meet federal security requirements.
End-to-end encryption is particularly important for file sharing and transfer scenarios. When properly implemented, even if data were intercepted during transmission, it would be unreadable to unauthorized parties.
Effective access control starts with verifying that every user is a U.S. person before granting any access to ITAR data. This verification process typically involves reviewing citizenship documentation and maintaining records of that verification for audit purposes.
Beyond identity verification, compliant environments implement several layers of protection:
Proving compliance requires comprehensive documentation of who accessed what data and when. Audit logs capture every access attempt, file modification, download, and administrative change. These logs are immutable—meaning they cannot be altered or deleted—to ensure their integrity during audits.
During an audit, you’ll demonstrate not just that controls exist, but that they’re working as intended. Regular log reviews and automated alerting help identify potential issues before they become violations.

ITAR compliant cloud services include security capabilities that go beyond standard commercial offerings. These features work together to create a protected environment for controlled data.
Network isolation prevents unauthorized systems from reaching ITAR data. By creating logically separate network zones, compliant environments contain potential breaches and prevent lateral movement by attackers. Firewalls and intrusion detection systems monitor traffic for suspicious activity around the clock.
Data Leak Prevention (DLP) tools actively monitor for unauthorized sharing or exfiltration of controlled data. DLP systems can detect when someone attempts to download sensitive files, share them outside approved channels, or copy them to unauthorized locations. This capability is particularly valuable for preventing accidental violations—like an employee unknowingly emailing ITAR data to a foreign colleague.
Automated retention policies ensure ITAR data is preserved for legally required periods while also managing secure disposal when data is no longer needed. Proper data lifecycle management reduces your overall risk footprint by eliminating unnecessary copies of controlled information.
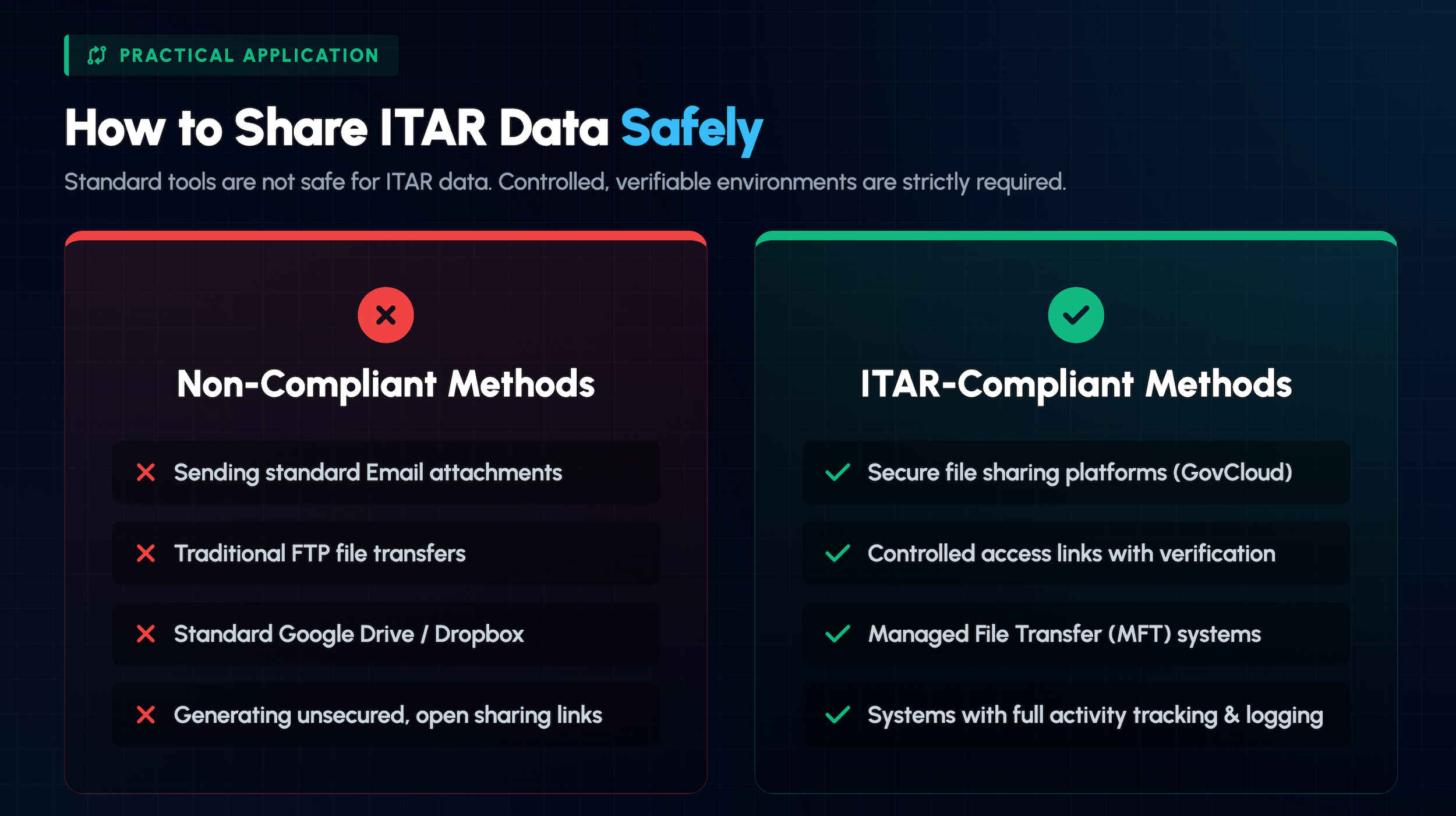
Sharing ITAR-controlled data presents unique challenges because every transmission represents a potential export. Standard email and consumer file-sharing services are not appropriate for controlled technical data.
ITAR compliant file sharing platforms enable collaboration among authorized U.S. persons while maintaining strict access controls. These systems typically include features like link expiration, download limits, and watermarking to maintain control over shared files. Every action—viewing, downloading, forwarding—is logged and auditable for compliance purposes.
Traditional methods like FTP and email attachments lack the security controls required for ITAR data. Compliant alternatives use encrypted connections and authenticated endpoints to ensure data remains protected throughout the transfer process. Managed file transfer (MFT) solutions designed for regulated industries often include built-in compliance features like automatic encryption and detailed transfer logging.

Several major cloud providers offer dedicated environments designed for ITAR and other government compliance requirements. These aren’t simply commercial clouds with extra settings—they’re physically and logically separated infrastructures with different operational models.
AWS GovCloud is an isolated cloud region operated exclusively by U.S. persons on U.S. soil. The environment is designed specifically for sensitive government workloads and supports both ITAR and FedRAMP requirements.
Azure Government is a physically separated instance of Microsoft’s cloud platform, offering a broad range of compliance certifications. The environment provides familiar Microsoft services—including Office 365 Government—in an infrastructure designed for U.S. government agencies and their contractors handling sensitive data.
Google Cloud’s Assured Workloads allows customers to create controlled environments where compliance requirements are automatically enforced. Assured Workloads includes data residency restrictions and personnel access controls appropriate for ITAR data, providing flexibility for organizations already invested in Google’s ecosystem.
Moving to ITAR compliant cloud storage requires careful planning and execution. The following steps outline a practical approach to getting it right.
Before selecting a platform, you’ll want to know exactly what data falls under ITAR control. This assessment involves reviewing your contracts, technical data, and business processes to identify all controlled information. Many organizations discover they have ITAR data in unexpected places during this process.
With your data inventory complete, evaluate cloud providers and environments that meet ITAR requirements. Consider factors like your existing technology investments, required services, and the provider’s compliance track record. Government cloud regions from major providers are typically the most straightforward path to compliance.
After selecting a platform, configure access controls, encryption settings, and security policies according to ITAR requirements. This step includes setting up U.S. person verification processes, implementing MFA, and establishing role-based access. Document your configurations thoroughly for future audits.
Compliance isn’t a one-time achievement—it requires ongoing attention. Establish continuous monitoring, regular log reviews, and periodic internal audits to ensure your environment remains compliant over time. This preparation also makes external audits much less stressful when they occur.
When evaluating managed service providers or cloud partners for ITAR compliance, consider the following criteria:
IT GOAT provides defense contractors with the expertise and support needed to implement and maintain ITAR compliant cloud storage. Our entirely U.S.-based team understands the unique requirements of the defense industry and delivers managed security services that keep your data protected and your organization audit-ready.
Book a Demo to discuss your ITAR compliance requirements with our team.
Yes, ITAR data can be stored in the cloud when the environment meets all regulatory requirements. Compliant cloud storage includes U.S.-based data centers, U.S. person access controls, and appropriate encryption. The key is selecting a cloud environment specifically designed for regulated workloads, such as AWS GovCloud or Azure Government.
ITAR violations can result in civil fines up to $1 million per violation, criminal prosecution with potential prison sentences, and debarment from future government contracts. The State Department’s Directorate of Defense Trade Controls (DDTC) enforces ITAR regulations and publishes consent agreements detailing violations and penalties.
ITAR and CMMC are separate but complementary frameworks. ITAR is a federal regulation focused on controlling the export of defense-related data, while CMMC establishes cybersecurity standards for the defense industrial base. An ITAR-compliant environment will satisfy many CMMC technical requirements, though the frameworks have different scopes and certification processes.
The primary difference is what each regulation covers and which agency oversees enforcement. ITAR, managed by the State Department, covers articles and data specifically designed for military applications. EAR (Export Administration Regulations), managed by the Commerce Department, covers “dual-use” items—commercial goods and technologies that could have military applications.
See the power of IT GOAT.
The world’s most advanced cybersecurity platform catered specifically to your business’ needs.
Keep up to date with our digest of trends & articles.
By subscribing, I agree to the use of my personal data in accordance with IT GOAT Privacy Policy. IT GOAT will not sell, trade, lease, or rent your personal data to third parties.

Mitigate All Types of Cyber Threats
Experience the full capabilities of our advanced cybersecurity platform through a scheduled demonstration. Discover how it can effectively protect your organization from cyber threats.

IT GOAT: Threat Intel & Cyber Analysis
We are experts in the field of cybersecurity, specializing in the identification and mitigation of advanced persistent threats, malware, and exploit development across all platforms.

Protect Your Business & Operations
Exceptional performance in the latest evaluations, achieving 100% prevention rate and providing comprehensive analytic coverage, unmatched visibility, and near-instant detection of threats.
We use cookies to enhance site performance and user experience. Your data stays private — we don’t sell your information or share it with unrelated third parties. To find out more about the cookies we use, view our Privacy Policy.