SOC 2 certification has become the gold standard for service organizations looking to prove their dedication to protecting client data.
As your trusted Managed IT Services partner, we guide organizations through every step of the SOC 2 certification process, transforming a potentially complex compliance journey into a strategic advantage for your business.
A prospect asks for your SOC 2 report, and suddenly you’re wondering whether compliance takes three months or three years. The answer depends on factors most organizations don’t consider until they’re already behind schedule.
This guide breaks down realistic timelines for both Type 1 and Type 2 audits, walks through each phase of the compliance process, and identifies the variables that accelerate or delay your path to a completed report.
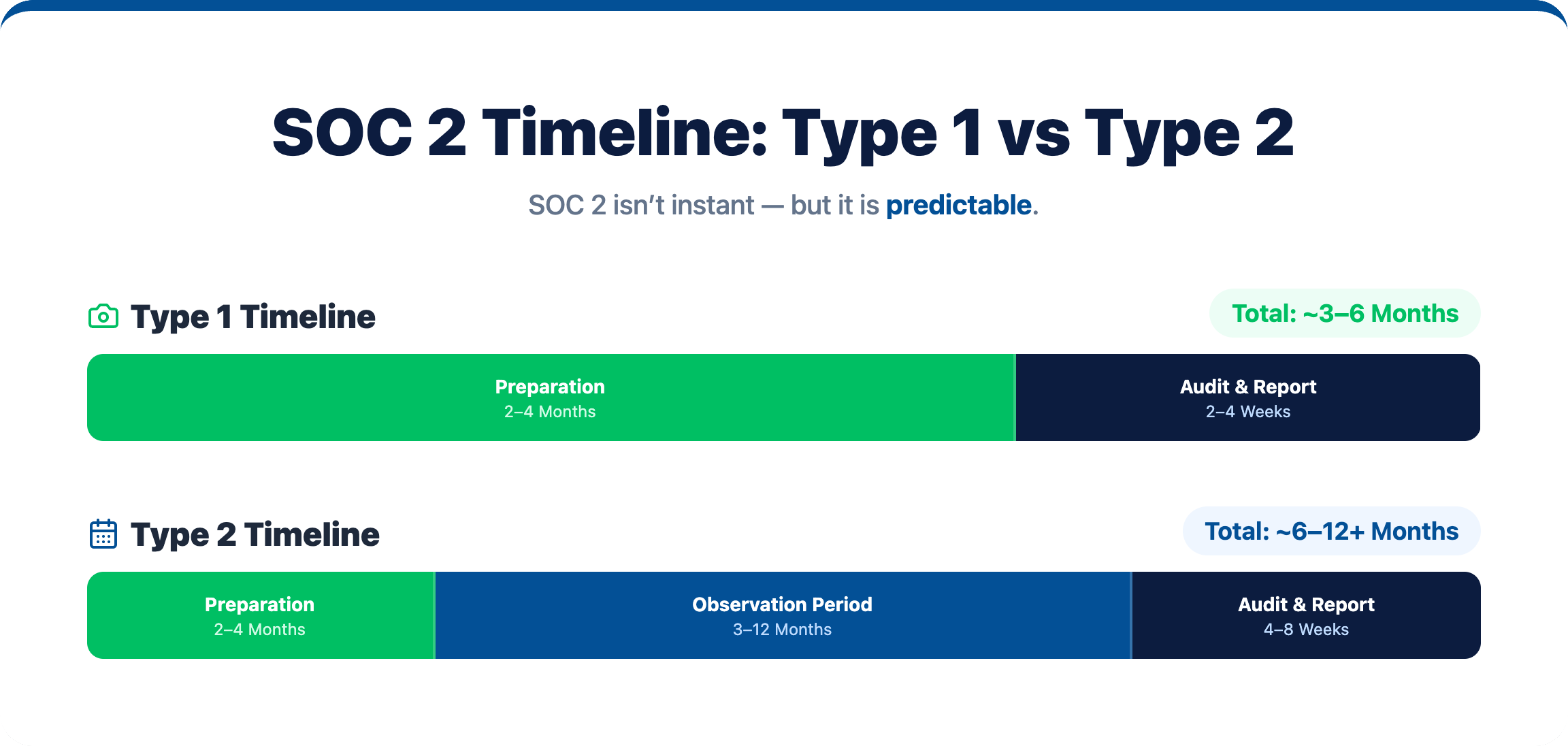
Most organizations complete SOC 2 compliance within 6 to 12 months, though your actual timeline depends heavily on your current security practices and which audit type you pursue. A Type 1 audit typically wraps up in 3 to 6 months since it only looks at your controls at one point in time. Type 2 audits take longer—usually 6 to 12 months—because auditors evaluate how well your controls work over an extended observation period.
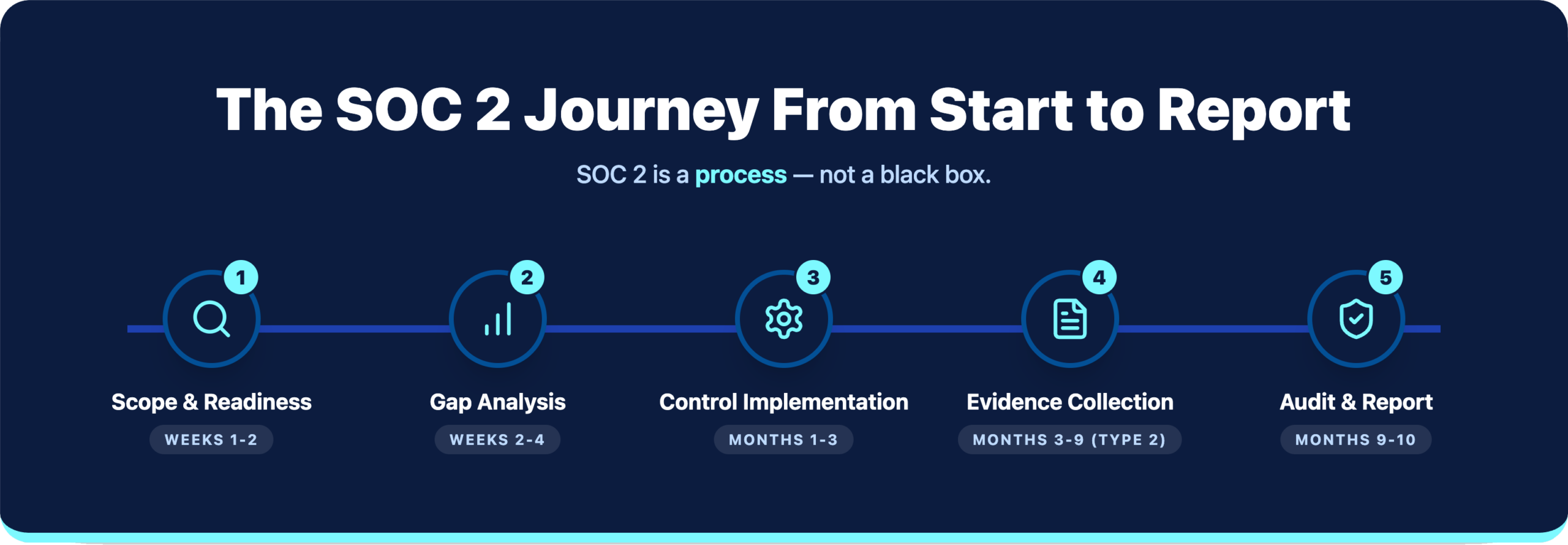

We begin with a thorough evaluation of your current security controls and procedures against SOC 2 requirements:
During this initial phase, we’ll work closely with your team to understand your business operations and define the scope of your SOC 2 certification.
With a clear roadmap in place, we focus on addressing gaps and implementing necessary controls:
Our team provides hands-on support throughout, ensuring all controls are properly implemented and documented according to SOC 2 standards.
Before engaging with external auditors, we conduct a thorough internal assessment:
This critical phase helps minimize surprises during the official audit and gives your team valuable experience in responding to auditor requests.
When it’s time for the official audit, we provide comprehensive support:
Our experts stand with you throughout the audit process, ensuring smooth communication with auditors and prompt resolution of any issues.
SOC 2 certification is not a one-time achievement but an ongoing commitment. Our maintenance services include:
We help you maintain compliance between audit cycles, ensuring your certification remains valid and your security posture continues to strengthen.
Three factors drive your total timeline: the audit type you choose, how mature your existing security program is, and how quickly your auditor can fit you into their schedule.
A Type 1 audit checks whether your controls are properly designed and in place at a specific moment—think of it as a snapshot. Organizations with decent security foundations often finish Type 1 preparation in 2 to 4 months, with the audit itself taking 2 to 4 weeks.
Type 1 works well when clients are pressing for compliance evidence right away, or when you want to test your readiness before committing to a longer Type 2 engagement.
Type 2 audits go deeper by evaluating whether your controls actually work over time. The observation period typically runs 3 to 12 months. Preparation mirrors Type 1, but then you operate your controls while collecting evidence before the auditor reviews everything.
Enterprise clients generally prefer Type 2 reports because they show sustained compliance rather than a single good day.
Smaller, specialized audit firms often move faster and offer more scheduling flexibility. Larger firms bring brand recognition but typically have longer lead times and more rigid processes.
To further streamline your compliance journey, consider leveraging professional audit services, ensuring your structure aligns perfectly with industry benchmarks, and keeps your enterprise secure.
Clear, jargon-free guidance throughout the process
We leverage advanced tools for efficient compliance management
Recognized for excellence with numerous industry awards, reflecting our commitment to delivering top-tier IT solutions. Our accolades showcase our dedication to innovation, quality service, and client satisfaction.

A Type 1 report assesses whether your controls are suitably designed at a specific point in time. A Type 2 report evaluates whether those controls are operating effectively over a period (typically 6-12 months). Most clients and partners value Type 2 reports more highly, as they demonstrate sustained compliance.
No. While Security is mandatory, you can select the other criteria based on your business operations and client expectations. We help you determine which criteria are most relevant for your organization.
While our team handles much of the specialized work, successful SOC 2 certification requires involvement from your IT, operations, and management teams. We’ll provide clear guidance on resource requirements during our initial planning.
Minor issues can often be addressed during the audit process. Significant deficiencies may require remediation before certification. Our thorough pre-audit assessment minimizes surprises, and we provide full support in addressing any findings.
Costs vary based on your organization’s size, complexity, and current security posture. Contact us for a customized quote that considers your specific requirements.
Our ongoing compliance services include regular control monitoring, updated risk assessments, and continuous improvement of security practices to ensure sustained compliance between annual audits.
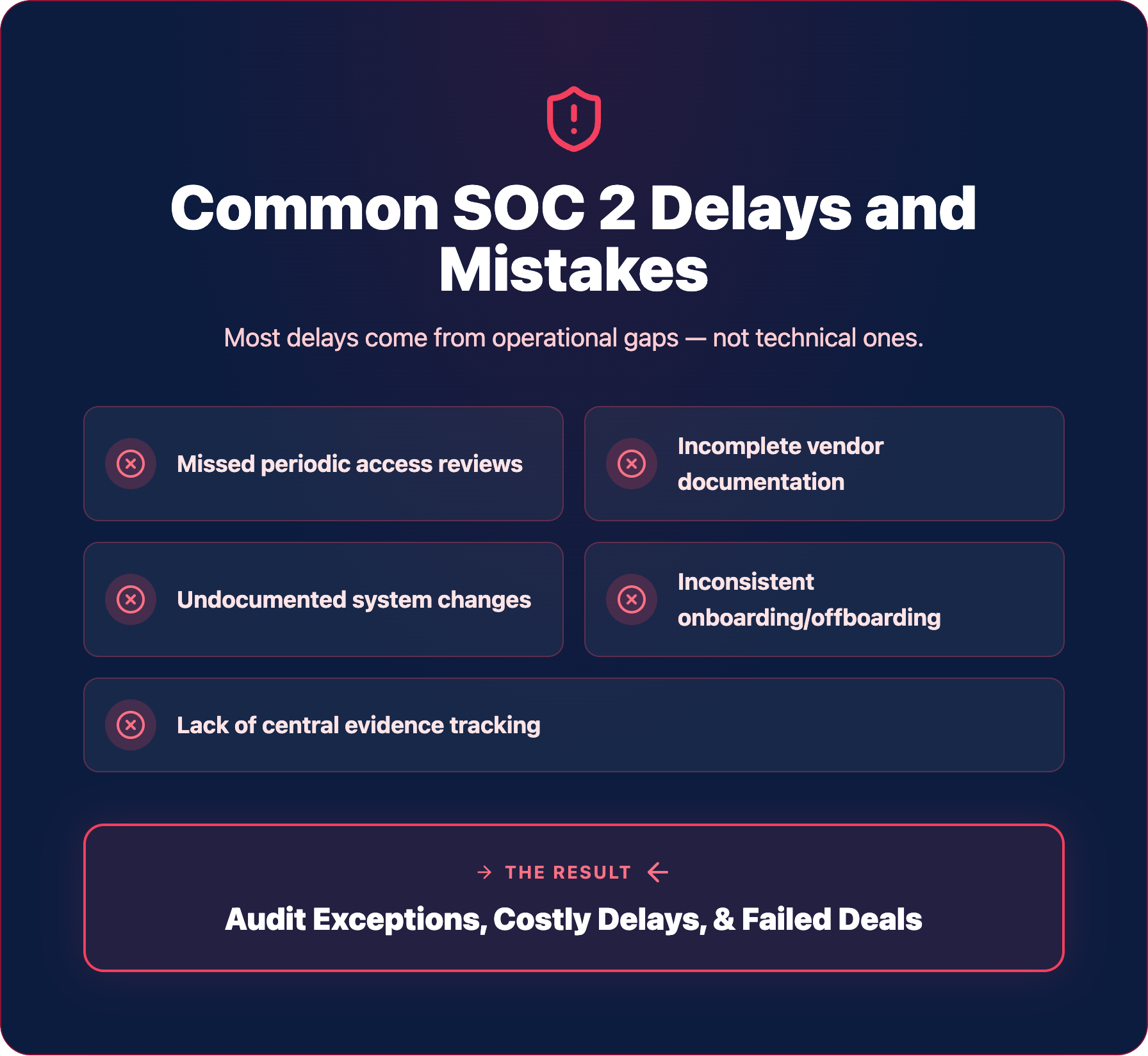
Avoiding common pitfalls keeps your timeline on track.
Auditors expect documented evidence of regular access reviews—typically quarterly for privileged accounts. Organizations that haven’t established this practice face gaps in their evidence trail that create audit exceptions.
Third-party vendors with access to your systems or data require documented security assessments. Missing vendor reviews raise concerns about your overall risk management program.
IT GOAT simplifies cybersecurity by integrating over 750+ enterprise apps to make sure your business runs smoothly.
SOC 2 certification is more than a compliance checkbox—it’s a powerful demonstration of your commitment to security and client trust. Our structured approach transforms this complex process into a strategic initiative that strengthens your business.
Contact us today for a free initial consultation to discuss your SOC 2 certification needs and discover how our services can help you achieve compliance efficiently and effectively.
We use cookies to enhance site performance and user experience. Your data stays private — we don’t sell your information or share it with unrelated third parties. To find out more about the cookies we use, view our Privacy Policy.