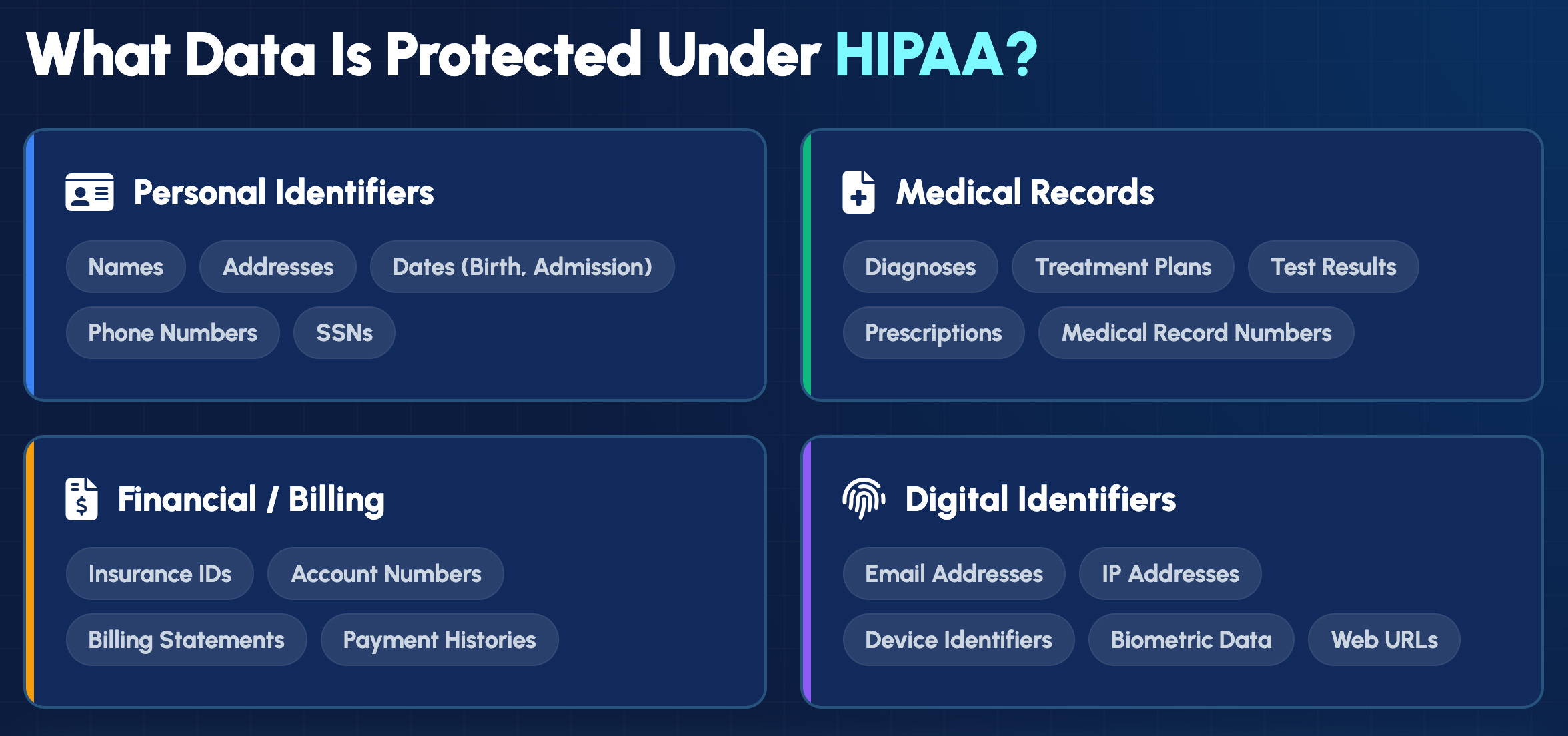
Understanding HIPAA privacy rule and compliance is crucial for any organization that deals with patient data. The HIPAA Privacy Rule establishes national standards aimed at protecting and regulating the use of personal health information.
Compliance not only involves safeguarding privacy but also implementing robust protocols to avoid costly breaches and maintain the trust of patients.
The Health Insurance Portability and Accountability Act (HIPAA) establishes national standards to protect sensitive patient health information from being disclosed without patient consent. Compliance isn’t optional—it’s essential for maintaining patient trust, avoiding costly penalties, and ensuring the integrity of your healthcare operations.


Administrative safeguards are the policies and procedures that manage security measure selection, development, and implementation.
Organizations require policies that prevent, detect, contain, and correct security violations. This includes conducting regular risk analyses and implementing measures to reduce identified risks to reasonable levels. A designated security official oversees these processes and maintains accountability for the organization’s security posture.
Not everyone in a healthcare organization requires access to all patient information. Workforce security policies ensure employees only access the ePHI necessary for their specific job functions. Authorization and supervision procedures govern how access is granted, modified, and terminated.
Healthcare organizations require plans for responding to emergencies that damage systems containing ePHI. This includes data backup plans, disaster recovery plans, and emergency mode operation plans. Regular testing of contingency plans verifies they’ll work when needed.

We begin with a thorough evaluation of your current systems, policies, and practices:
This phase establishes your compliance baseline and identifies priority areas for remediation.
Based on assessment findings, we develop a customized remediation plan:
We work alongside your team to execute the remediation plan:
Technical safeguard implementation
Administrative safeguard implementation
Physical safeguard implementation
We ensure all compliance measures are properly documented and effective:
Proper access controls directly support healthcare privacy by ensuring only authorized individuals view patient information. The principle of “minimum necessary” guides access decisions.
Access rights align with job functions so employees see only the PHI their roles require. A billing specialist doesn’t require access to clinical notes, while a nurse doesn’t require access to collection records.
MFA requires users to verify their identity through multiple methods before gaining access. Combining something you know (password) with something you have (phone) or something you are (fingerprint) significantly reduces unauthorized access risk.
Automatic logoff features protect unattended workstations. When a clinician steps away to see a patient, the system locks itself rather than leaving records exposed.
Contact us today for a confidential consultation and take the first step toward comprehensive HIPAA compliance and peace of mind.
Our relationship doesn't end with implementation—we provide continuous monitoring and support.
Our methodologies integrate compliance measures with minimal impact on your day-to-day operations.
Physical safeguards protect electronic systems and the buildings housing them from unauthorized access, natural hazards, and environmental threats.
Policies limit physical access to facilities where ePHI systems reside. Depending on the facility’s risk profile, this might include badge access systems, visitor logs, and security personnel.
Workstation use policies govern how devices accessing ePHI are positioned and secured. A computer screen visible to the waiting room presents different risks than one in a private office.
Before disposing of or repurposing devices that contained ePHI, organizations properly sanitize them. Simply deleting files isn’t sufficient—hard drives require secure wiping or physical destruction.
Recognized for excellence with numerous industry awards, reflecting our commitment to delivering top-tier IT solutions. Our accolades showcase our dedication to innovation, quality service, and client satisfaction.

In the context of healthcare, FWA stands for Fraud, Waste, and Abuse. These terms refer to different kinds of erroneous behaviors that compromise the integrity of healthcare systems. Fraud involves deliberate deception or misrepresentation to gain unauthorized benefits, while waste refers to the overutilization or misuse of resources without intent to deceive. Abuse involves behaviors that may result in unnecessary costs to the health care system but are not characterized by deceit. Addressing FWA is crucial for cost control, quality improvement, and ensuring that resources are available for genuine needs.
TPO in HIPAA stands for Treatment, Payment, and Healthcare Operations. These are specific categories under the Health Insurance Portability and Accountability Act (HIPAA) where protected health information (PHI) can be used or disclosed without patient authorization. ‘Treatment’ is related to the provision, coordination, or management of healthcare services. ‘Payment’ refers to activities undertaken by a provider to obtain payment for services. ‘Healthcare operations’ encompass a range of activities such as quality assessment, training, licensing, and insurance underwriting. TPO provisions allow for efficient functioning of healthcare services while maintaining patient privacy.
There is no formal “certification” for HIPAA compliance in the same sense as a certification for other regulated industries. Often, organizations conduct internal or third-party audits to demonstrate compliance with HIPAA Security and Privacy Rules. However, professional training programs and courses that offer certificates indicating that IT professionals or employees have received HIPAA training are typically valid as long as the educational content is considered current. Courses and training should be refreshed regularly, as HIPAA regulations and technologies evolve. Continuous education ensures ongoing compliance with the latest requirements and best practices.
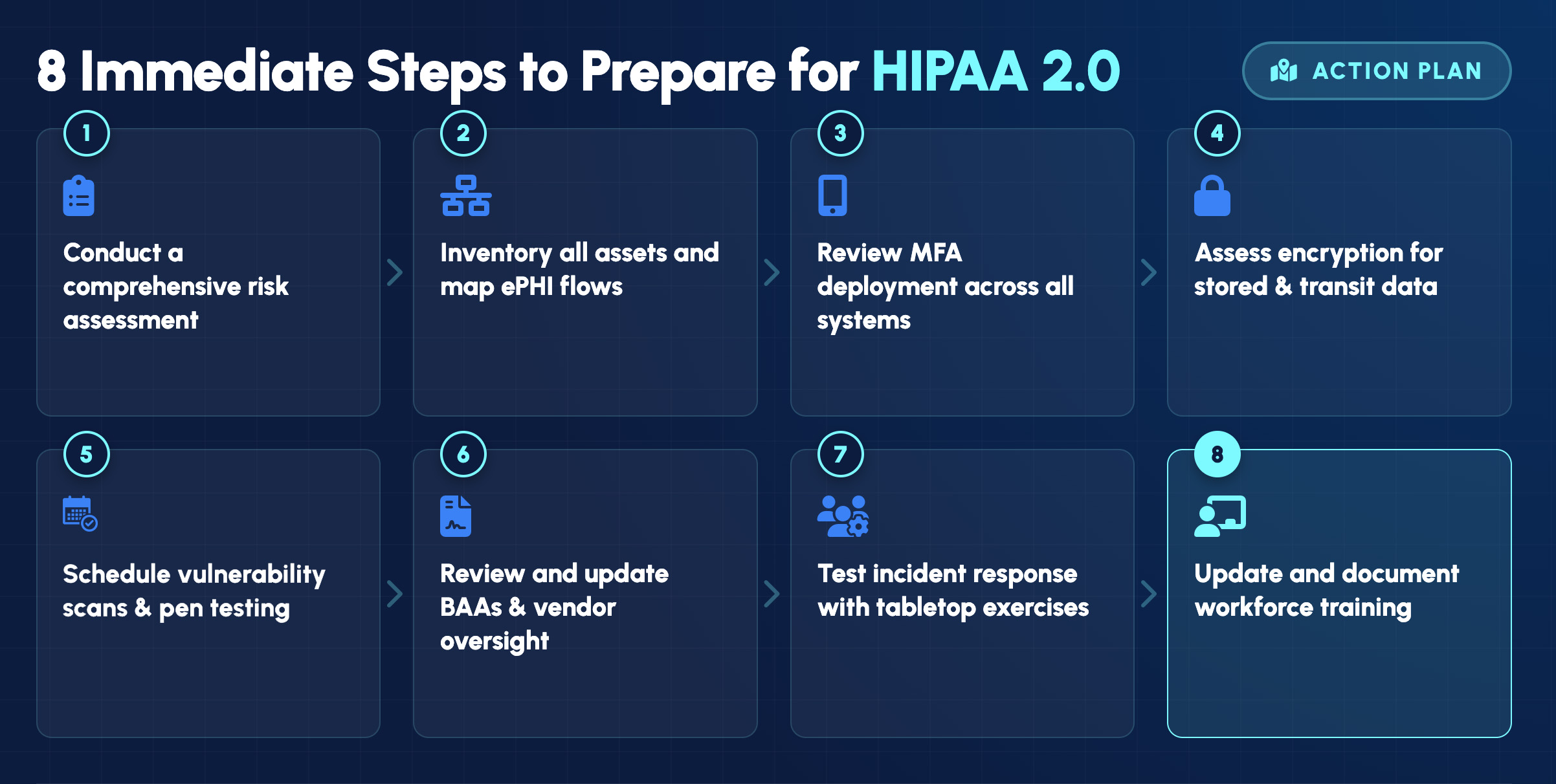
To comply with HIPAA, organizations must implement a comprehensive set of safeguards that include both administrative, physical, and technical protections to ensure the confidentiality, integrity, and availability of electronic protected health information (ePHI). Key measures include:
1. Conducting regular risk assessments to identify potential vulnerabilities.
2. Instituting access controls to ensure that only authorized personnel have access to ePHI.
3. Implementing encryption and secure communication protocols.
4. Providing ongoing training and awareness programs for staff.
5. Having documented policies and procedures in place for managing and mitigating potential breaches.
HIPAA, which stands for the Health Insurance Portability and Accountability Act, is a significant piece of legislation enacted in 1996 to protect the privacy and security of PHI. There is a common misconception or typo where people refer to “HIPPA” instead of “HIPAA.” It’s crucial to use the correct acronym HIPAA when discussing compliance, risks, or any security measures associated with the act in discussions or official documentation. IT GOAT recommends organizations ensure all staff are educated on the correct terminology as a best practice to reflect professional accuracy and integrity within the healthcare industry.
IT GOAT simplifies cybersecurity by integrating over 750+ enterprise apps to make sure your business runs smoothly.
Incident response encompasses detecting, responding to, and recovering from security incidents involving PHI.
Speed of detection plays a major role in breach impact. Industry reports show that the average time to identify and contain a breach is often 200+ days, giving attackers extended access to sensitive systems.
For healthcare organizations, delayed detection increases:
Organizations with continuous monitoring and incident response capabilities significantly reduce detection time, limiting both financial damage and compliance exposure.
A breach is unauthorized acquisition, access, use, or disclosure of PHI that compromises security or privacy. HIPAA presumes any unauthorized access constitutes a breach unless the organization proves otherwise through a risk assessment.
Breach notifications to affected individuals require delivery within 60 days of discovery. Breaches affecting 500 or more individuals also require notification to prominent media outlets and immediate reporting to HHS.
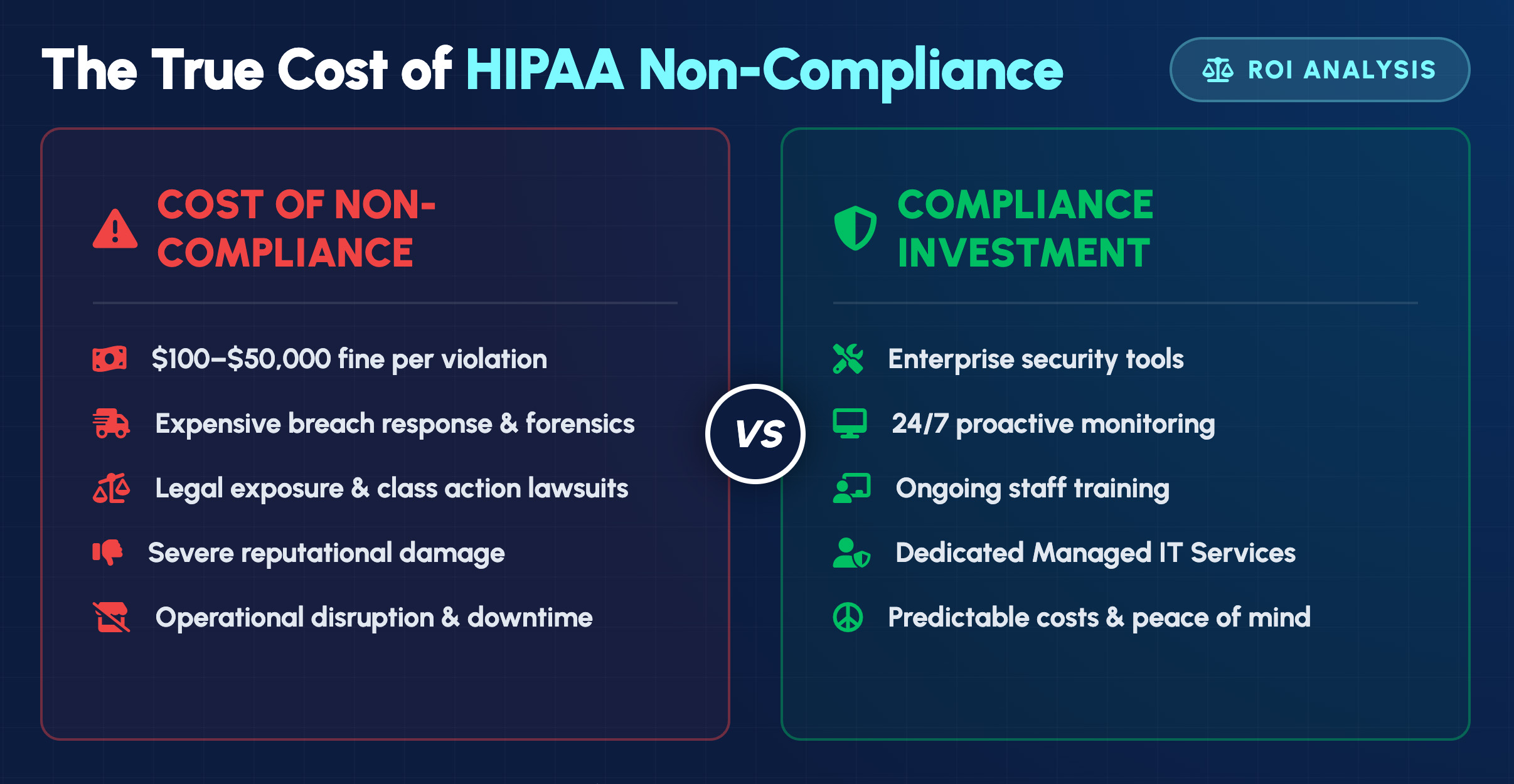

Beyond meeting regulatory requirements, proper HIPAA compliance delivers significant benefits:
Compliance is not just a legal obligation but a commitment to protecting patient privacy. Leveraging expertise in cybersecurity, like that of IT GOAT, ensures your organization employs the best practices to secure PHI.
By prioritizing compliance, conducting regular audits, and implementing robust security measures, you can effectively mitigate risks and prepare for evolving regulatory landscapes.
Let IT GOAT guide you through the complexities of HIPAA with tailored solutions that uphold privacy and enhance security.
We use cookies to enhance site performance and user experience. Your data stays private — we don’t sell your information or share it with unrelated third parties. To find out more about the cookies we use, view our Privacy Policy.