Winning DoD contracts increasingly depends on one thing many small businesses haven’t tackled yet: CMMC certification. The framework protects sensitive defense information across the supply chain, and contractors without certification will find themselves locked out of opportunities their competitors can pursue.
This guide walks through the complete CMMC Level 2 compliance process, from identifying whether your business handles Controlled Unclassified Information to selecting an assessor and maintaining certification after you’ve earned it.

CMMC 2.0 compliance for small businesses starts with identifying whether your company handles Federal Contract Information (FCI) or Controlled Unclassified Information (CUI), then implementing the security controls that match your data type. The Cybersecurity Maturity Model Certification is a DoD framework that protects sensitive defense information across the entire supply chain. Every contractor and subcontractor touching defense work falls somewhere within this framework.
The program organizes requirements into three maturity levels. Level 1 covers basic cyber hygiene with 17 practices for businesses handling FCI. Level 2 aligns with NIST SP 800-171 and includes 110 security controls for organizations handling CUI. Level 3 addresses advanced persistent threats and applies to contractors working with the most sensitive programs.
A few terms come up repeatedly in CMMC documentation:
Not every defense contractor requires Level 2 certification. The determining factor is whether your organization processes, stores, or transmits CUI as part of contract work.
Any contractor that touches CUI during contract performance falls under Level 2 requirements. This includes businesses receiving technical specifications, engineering data, or other sensitive information marked as CUI. Even temporary storage or access through a prime contractor’s systems triggers the same obligations.
Subcontractors often assume CMMC applies only to prime contractors. However, requirements flow down through the entire supply chain. If a prime contractor shares CUI with your organization through email, file transfers, or shared systems, you inherit the same compliance obligations they carry.
CMMC requirements will appear in contract solicitations as the DoD phases in the program. Businesses that prepare early position themselves to compete for contracts that competitors without certification cannot pursue. Starting now also spreads the compliance investment over time rather than creating a last-minute scramble.
Level 2 certification requires implementing all 110 security practices defined in NIST SP 800-171, organized across 14 control families. Each family addresses a specific aspect of your security program.
| Control Family | What It Covers |
|---|---|
| Access Control | Limiting system access to authorized users and transactions |
| Awareness and Training | Ensuring personnel understand security responsibilities |
| Audit and Accountability | Creating and reviewing logs to trace user actions |
| Configuration Management | Establishing baseline configurations for systems |
| Identification and Authentication | Verifying identities before granting access |
| Incident Response | Detecting, reporting, and responding to security events |
| Maintenance | Performing system maintenance while protecting CUI |
| Media Protection | Controlling physical and digital media containing CUI |
| Personnel Security | Screening individuals and managing access changes |
| Physical Protection | Limiting physical access to systems and facilities |
| Risk Assessment | Periodically assessing organizational risk |
| Security Assessment | Monitoring security controls for effectiveness |
| System and Communications Protection | Protecting communications at system boundaries |
| System and Information Integrity | Identifying and correcting system flaws promptly |
Working through CMMC compliance becomes more manageable when broken into discrete steps. The following checklist provides a practical roadmap for small businesses with limited IT resources.
Start by mapping where CUI enters your organization, how it flows through your systems, and where it ultimately resides. Review your contracts and speak with contracting officers to confirm which information qualifies as CUI. This mapping exercise defines everything that follows.
Document which systems, networks, applications, and personnel interact with CUI. Many small businesses reduce their compliance burden by isolating CUI to a smaller segment of their environment rather than applying controls across the entire organization.
Compare your current security posture against each of the 110 NIST SP 800-171 controls. A gap analysis reveals where you already meet requirements and where remediation work remains. Several CMMC self-assessment tools and spreadsheet templates can help structure this process.
The System Security Plan (SSP) documents how your organization implements each control. Think of it as the master reference explaining your security program to assessors. Every control requires a description of how you meet it or why it doesn’t apply to your environment.
The POA&M captures gaps identified during your assessment along with your remediation timeline. Assessors expect to see a realistic plan for addressing deficiencies, including responsible parties, target completion dates, and resource requirements.

Deploy the technologies required to meet CMMC controls:
Written policies formalize your security program and demonstrate organizational commitment. Develop policies addressing acceptable use, access management, incident response, media handling, and each control family. Procedures then explain how staff execute those policies day to day.
Security awareness training covers CUI handling procedures, phishing recognition, password hygiene, and incident reporting. Training records become evidence during your assessment, so document attendance and completion for all personnel with system access.
Use the NIST SP 800-171 assessment methodology to score your compliance before engaging a third-party assessor. This internal assessment identifies remaining gaps and builds confidence that you’re ready for the formal evaluation.
CMMC Third-Party Assessment Organizations (C3PAOs) are accredited to conduct official Level 2 assessments. The Cyber AB marketplace lists all authorized assessors, allowing you to compare options and select one that fits your timeline and budget.
The C3PAO reviews your documentation, interviews key personnel, and examines technical evidence for each control. Assessments may occur on-site, virtually, or through a hybrid approach depending on your environment and the assessor’s methodology.
If the assessment identifies deficiencies, you’ll have an opportunity to remediate and demonstrate compliance. Once all requirements are satisfied, the C3PAO issues your certification.

Beyond completing the checklist, several preparation activities increase your chances of a smooth assessment experience.
Compile your SSP, POA&M, security policies, network diagrams, asset inventories, and any prior assessment results. Assessors request these documents early in the process, so having them organized and accessible saves time and reduces stress.
Simulating the assessment process internally or with a consultant reveals weaknesses before they become findings. Walk through each control as if you were the assessor, asking for evidence and interviewing staff about their responsibilities.
Organize screenshots, configuration exports, training records, and policy documents mapped to specific controls. When an assessor asks how you implement a particular requirement, you want to produce supporting evidence within minutes rather than hours.
Key personnel will participate in interviews during the assessment. Ensure they understand their role in the security program and can speak confidently about the controls they manage or use daily.
Several tool categories simplify compliance tracking and reduce the administrative burden on small teams.
Automated platforms guide you through each NIST 800-171 control, calculate your compliance score, and generate gap reports. These tools standardize the assessment process and help ensure you don’t overlook requirements.
Cloud-based solutions enable collaboration across distributed teams, which proves especially valuable for organizations with remote workers or multiple locations. Team members can update control status, upload evidence, and track remediation progress from anywhere.
For organizations preferring manual tracking, CMMC checklist Excel templates and control spreadsheets provide a structured format without software costs. These templates typically map each control to documentation requirements and implementation guidance.
Continuous monitoring tools, including SIEM platforms and vulnerability scanners, support ongoing compliance rather than point-in-time assessments. These solutions also generate evidence of your security posture for assessors.

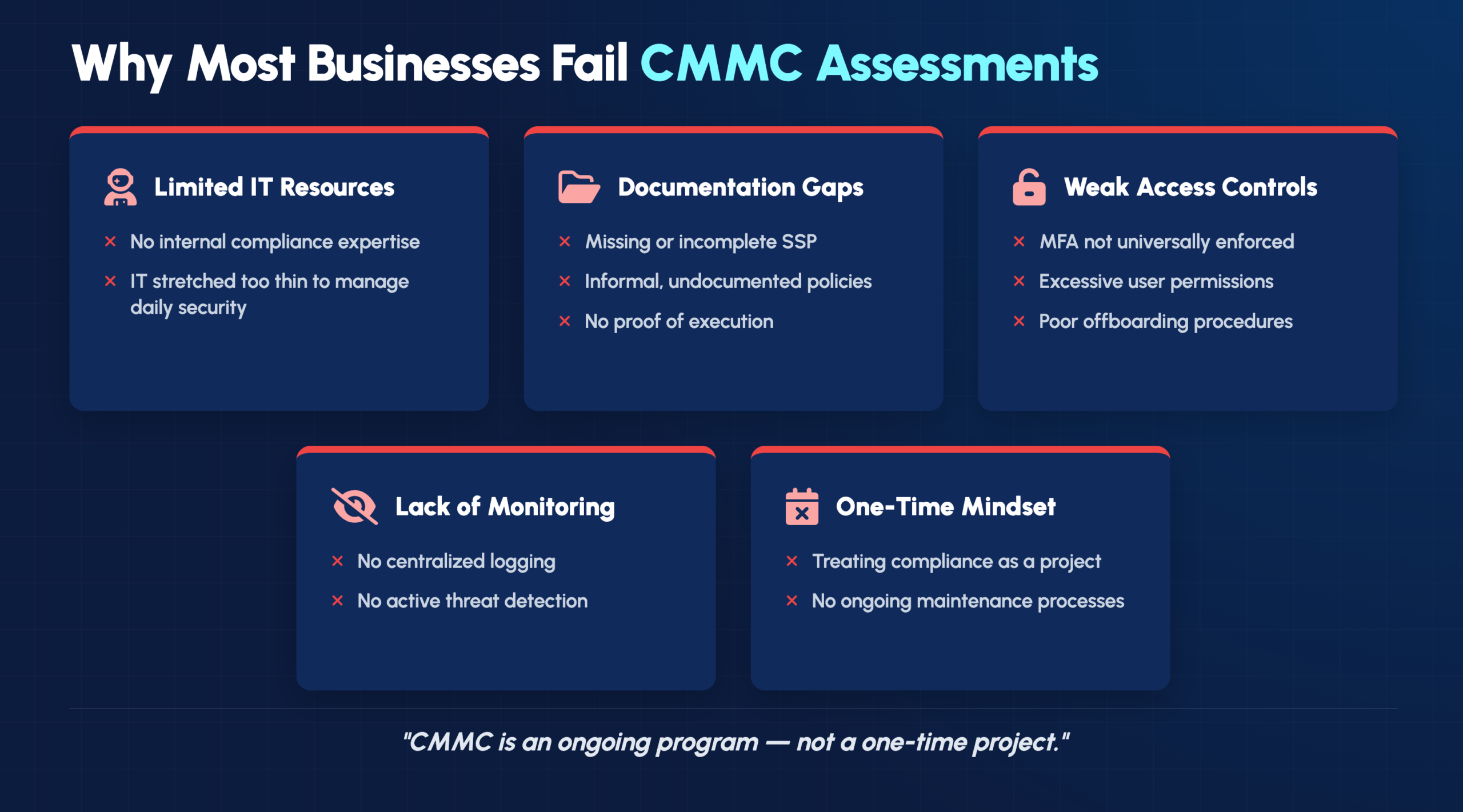
Small businesses frequently encounter similar obstacles during the compliance journey.
Many small businesses lack dedicated security staff. Partnering with a managed service provider experienced in CMMC compliance provides access to expertise without hiring full-time specialists.
Assessors expect comprehensive documentation, yet many organizations operate with informal or outdated policies. Starting documentation early and using standardized templates prevents last-minute scrambling.
Access control deficiencies appear frequently in assessments. Implementing role-based access, enforcing least privilege, and deploying multi-factor authentication address foundational requirements affecting multiple control families.
CMMC compliance isn’t a one-time achievement. Organizations that treat it as a checkbox exercise often struggle during reassessment. Establishing continuous monitoring practices maintains compliance between formal assessments.
Compliance costs vary significantly based on organization size, existing security maturity, and scope complexity.
| Cost Category | What Influences It |
|---|---|
| Assessment and certification fees | Organization size, scope complexity, assessor selection |
| Technology investments | Current infrastructure, security tool gaps, enclave requirements |
| Consulting and managed services | Internal expertise, remediation scope, ongoing support |
| Maintenance expenses | Annual assessments, training, tool subscriptions |
Many small businesses find that engaging a managed service provider or CMMC consultant reduces total cost by avoiding missteps and accelerating the timeline.
Certification marks the beginning of ongoing compliance rather than the end. The DoD requires annual affirmations from a senior company official confirming continued compliance.
Maintaining certification involves performing annual self-assessments, updating documentation when systems or processes change, conducting regular security awareness training, monitoring systems continuously for security events, and reviewing policies to reflect evolving threats.
Navigating CMMC compliance while running your business creates competing demands on limited resources. IT GOAT’s U.S.-based security professionals provide the expertise and proactive monitoring that small businesses rely on to achieve and maintain certification.
Book a consultation to discuss your CMMC compliance roadmap.
Level 2 certification remains valid for three years. Organizations provide annual affirmations confirming continued compliance throughout that period.
Organizations that don’t pass receive findings detailing deficiencies. After remediation, you can request reassessment of the specific areas requiring correction.
Yes, MSPs can implement and manage security controls on your behalf. However, the contractor remains ultimately responsible for compliance and certification.
Commercial item contractors may still require certification if their contracts involve CUI. Review contract clauses and consult with your contracting officer to confirm requirements.
CUI is identified through contract markings and the CUI Registry. When uncertain, coordinate with your contracting officer to clarify which information requires protection.
Level 1 allows annual self-assessment with results submitted to SPRS. Level 2 requires assessment by an accredited C3PAO, though some contracts may permit self-assessment for limited CUI exposure.
See the power of IT GOAT.
The world’s most advanced cybersecurity platform catered specifically to your business’ needs.
Keep up to date with our digest of trends & articles.
By subscribing, I agree to the use of my personal data in accordance with IT GOAT Privacy Policy. IT GOAT will not sell, trade, lease, or rent your personal data to third parties.

Mitigate All Types of Cyber Threats
Experience the full capabilities of our advanced cybersecurity platform through a scheduled demonstration. Discover how it can effectively protect your organization from cyber threats.

IT GOAT: Threat Intel & Cyber Analysis
We are experts in the field of cybersecurity, specializing in the identification and mitigation of advanced persistent threats, malware, and exploit development across all platforms.

Protect Your Business & Operations
Exceptional performance in the latest evaluations, achieving 100% prevention rate and providing comprehensive analytic coverage, unmatched visibility, and near-instant detection of threats.
We use cookies to enhance site performance and user experience. Your data stays private — we don’t sell your information or share it with unrelated third parties. To find out more about the cookies we use, view our Privacy Policy.