ISO 27001 is the internationally recognized standard for information security management. It provides organizations with a systematic framework for ensuring the confidentiality, integrity, and availability of sensitive information.
This comprehensive approach to security management has become essential in today’s digital landscape where data breaches and cyber threats continue to evolve in sophistication.
Our ISO 27001 certification services provide a structured pathway to achieving internationally recognized information security standards, ensuring your business remains resilient against evolving cyber threats.

ISO 27001 is the internationally recognized standard for Information Security Management Systems (ISMS). Published by the International Organization for Standardization, it defines requirements for establishing, implementing, maintaining, and continually improving a structured approach to managing information security risks. Critically, ISO 27001 is an organizational maturity standard — not a purely technical one. Achieving certification means demonstrating that security governance is embedded across people, processes, and technology, not just that certain IT tools are in place.
As of October 2025, all organizations pursuing or renewing ISO 27001 certification must conform to the 2022 edition of the standard. The 2013 version has expired and is no longer accepted for new certifications or renewals. Any organization operating under a 2013-based certification needs to either have completed its transition or is now out of compliance with the standard.
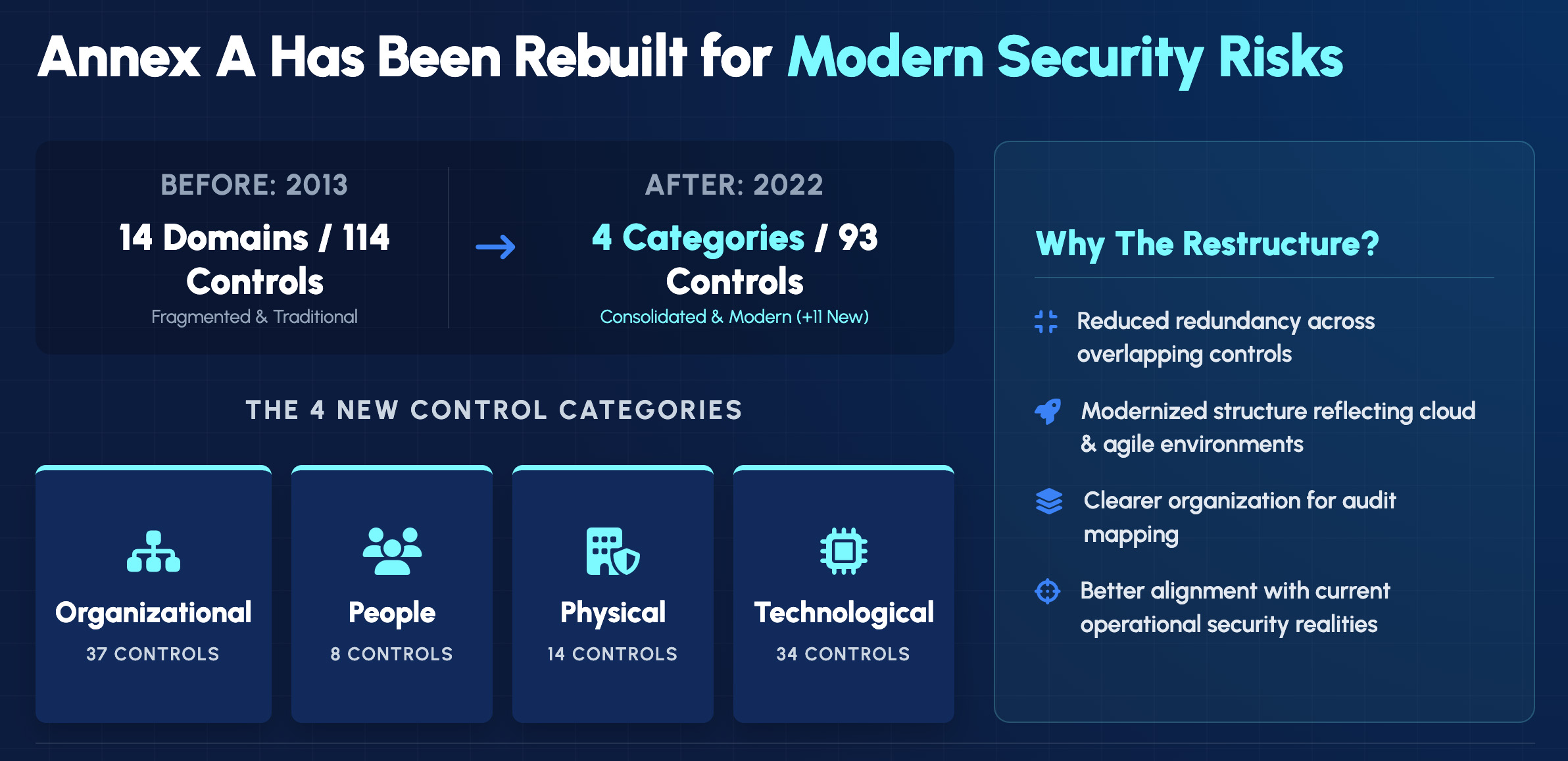
For organizations seeking new certification in 2026, there is no choice — audits are conducted against the 2022 standard exclusively. For organizations whose 2013-based certifications expired without transition, the path forward requires a full certification audit against the 2022 edition. There is no shortcut or grandfather provision available under the current IAF framework.
Clause 4 requires organizations to understand the internal and external environment in which the ISMS operates. This means identifying factors that affect information security objectives, defining which parts of the organization and which assets fall within the ISMS scope, and identifying interested parties — customers, regulators, partners, and others — whose requirements must be considered. A well-defined scope is foundational to everything that follows. Scope that is too narrow creates compliance gaps; scope that is too broad creates implementation burdens that undermine effectiveness.
Clause 5 establishes that ISO 27001 is not an IT initiative — it requires visible, active commitment from top management. Leadership must establish and endorse an information security policy, ensure that ISMS objectives align with organizational direction, assign clear roles and responsibilities for information security, and demonstrate ongoing engagement with the ISMS. Auditors specifically look for evidence of leadership involvement, not just policy documents signed by an executive. Organizations where security is delegated entirely to IT without executive engagement consistently struggle with this clause.
Clause 6 requires organizations to identify and address risks and opportunities that could affect the ISMS’s ability to achieve its objectives. This involves conducting a systematic risk assessment — identifying threats and vulnerabilities, evaluating potential impacts and likelihoods, and selecting risk treatment options. Organizations must also set measurable information security objectives that are consistent with the security policy and the risk assessment findings. Risk assessment is not a one-time exercise; it must be repeated when significant changes occur and at planned intervals.


Initial Assessment and Gap Analysis
Leadership Engagement and Scope Definition
Resource Allocation and Project Planning
Risk Assessment and Treatment
Security Controls Implementation
Policy and Procedure Development
Staff Training and Awareness
Internal Audits
Management Review
Pre-certification Assessment
Stage 1 Audit
Stage 2 Audit
Certification Achievement
Surveillance Audits
ISMS Maintenance
Recertification
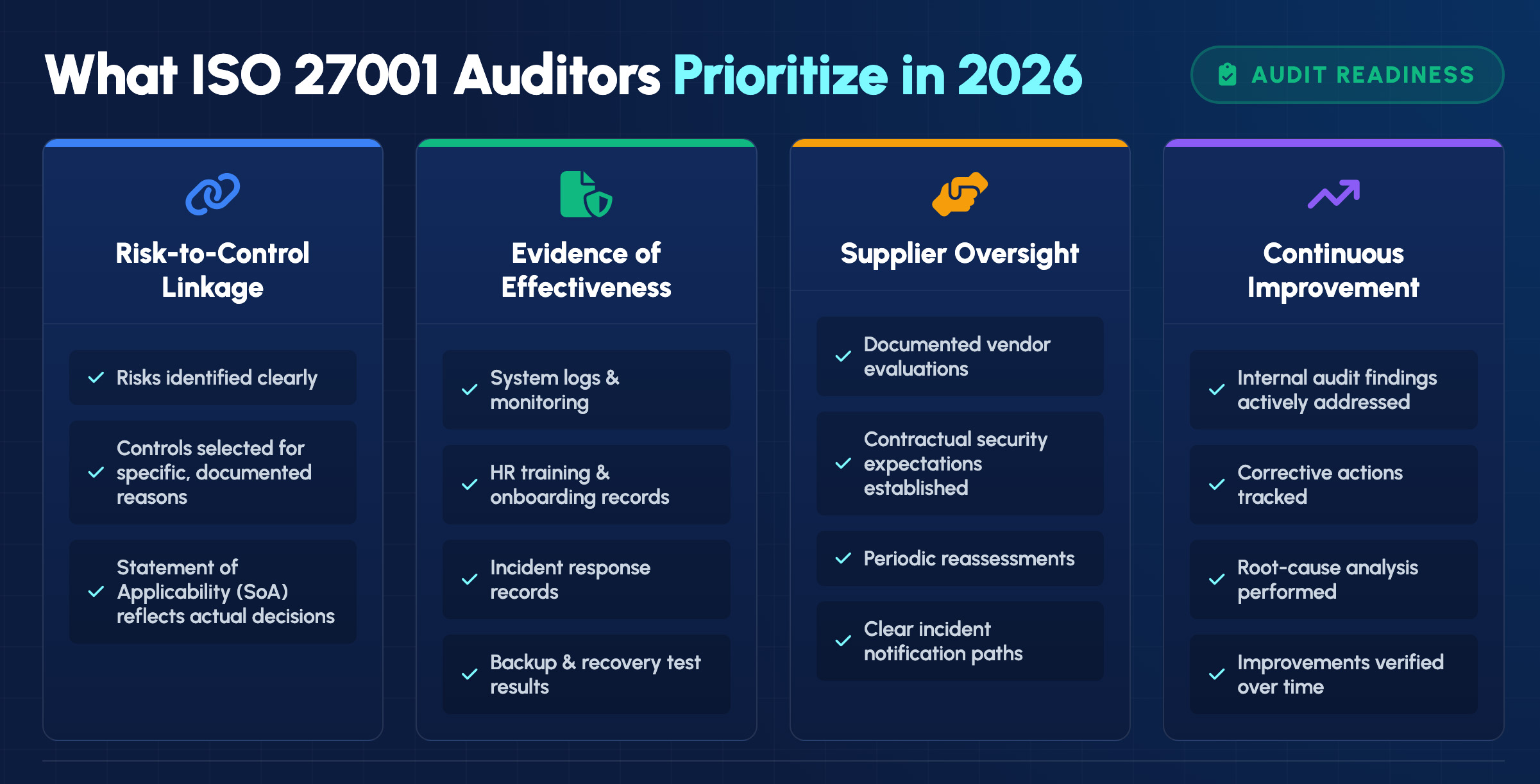
ISO 27001 auditors in 2026 are looking for organizational maturity, not checkbox compliance. An organization that can produce a policy document for every requirement but cannot demonstrate that policies translate into operational practice will struggle in a certification audit. Understanding auditor priorities helps organizations direct their preparation efforts appropriately.
The 37 organizational controls address governance and management frameworks that define how the organization approaches information security. This category includes information security policies, asset management practices, access control policies, supplier relationship management, incident management procedures, and compliance requirements. These controls establish the rules and structures under which all other security activity operates.
The 8 people controls address the human dimension of information security — the workforce practices, training programs, and behavioral expectations that reduce the risk of human error and insider threat. This category covers pre-employment screening, terms and conditions of employment, security awareness and training programs, and disciplinary processes for security violations. Despite being the smallest category by count, people controls are frequently where security programs succeed or fail in practice.
The 14 physical controls address the security of facilities, equipment, and the physical environment where information is stored and processed. This category includes requirements for secure areas with appropriate access controls, equipment security practices that protect against theft and tampering, clear desk and clear screen policies that reduce the risk of physical data exposure, and controls for supporting utilities and cabling.
The 34 technological controls address the technical mechanisms that protect information systems and data. This is the broadest technical category and covers endpoint security, user access rights management, privileged access management, cryptography, network security, web filtering, secure development practices, data leakage prevention, and monitoring and logging. Many of the new controls introduced in the 2022 edition fall within this category, reflecting the standard’s updated focus on cloud environments, modern application development, and advanced threat management.
Our specialized team brings extensive experience in information security management and ISO 27001 implementation across diverse industries.
Efficient processes that optimize time and resource investment
Alignment of security measures with business objectives
Recognized for excellence with numerous industry awards, reflecting our commitment to delivering top-tier IT solutions. Our accolades showcase our dedication to innovation, quality service, and client satisfaction.

ISO 27001 certification is a globally recognized standard that outlines best practices for an information security management system (ISMS). Organizations of all sizes and sectors can benefit from obtaining this certification. However, it is particularly advantageous for businesses that handle sensitive data, such as those in finance, healthcare, and IT, where data breaches could have severe consequences.
ISO 27001 and ISO 27002 are both part of the ISO/IEC 27000 family of standards focused on information security management, but they serve different purposes and should not be confused. Understanding their distinctions is crucial for organizations aiming to build a robust information security framework.
The cost of ISO 27001 certification varies based on several factors, including:
A small to medium-sized business might invest anywhere from $30,000 to $100,000+ for the entire certification process, including implementation and audit costs. Larger organizations or those with complex environments may see higher costs.
We offer flexible engagement models and can provide a detailed cost estimate after conducting an initial assessment of your current security posture and requirements.
ISO 27001 certification requires ongoing maintenance and periodic reassessment:
Our post-certification support services help ensure your ISMS remains effective and continues to evolve with changing threats and business needs. We can provide varying levels of ongoing support, from periodic check-ins to comprehensive managed security services.
The journey to ISO 27001 certification begins with understanding your current position and defining clear objectives. Our recommended first steps include:
Contact us today to arrange your initial consultation and take the first step toward world-class information security management.
IT GOAT simplifies cybersecurity by integrating over 750+ enterprise apps to make sure your business runs smoothly.
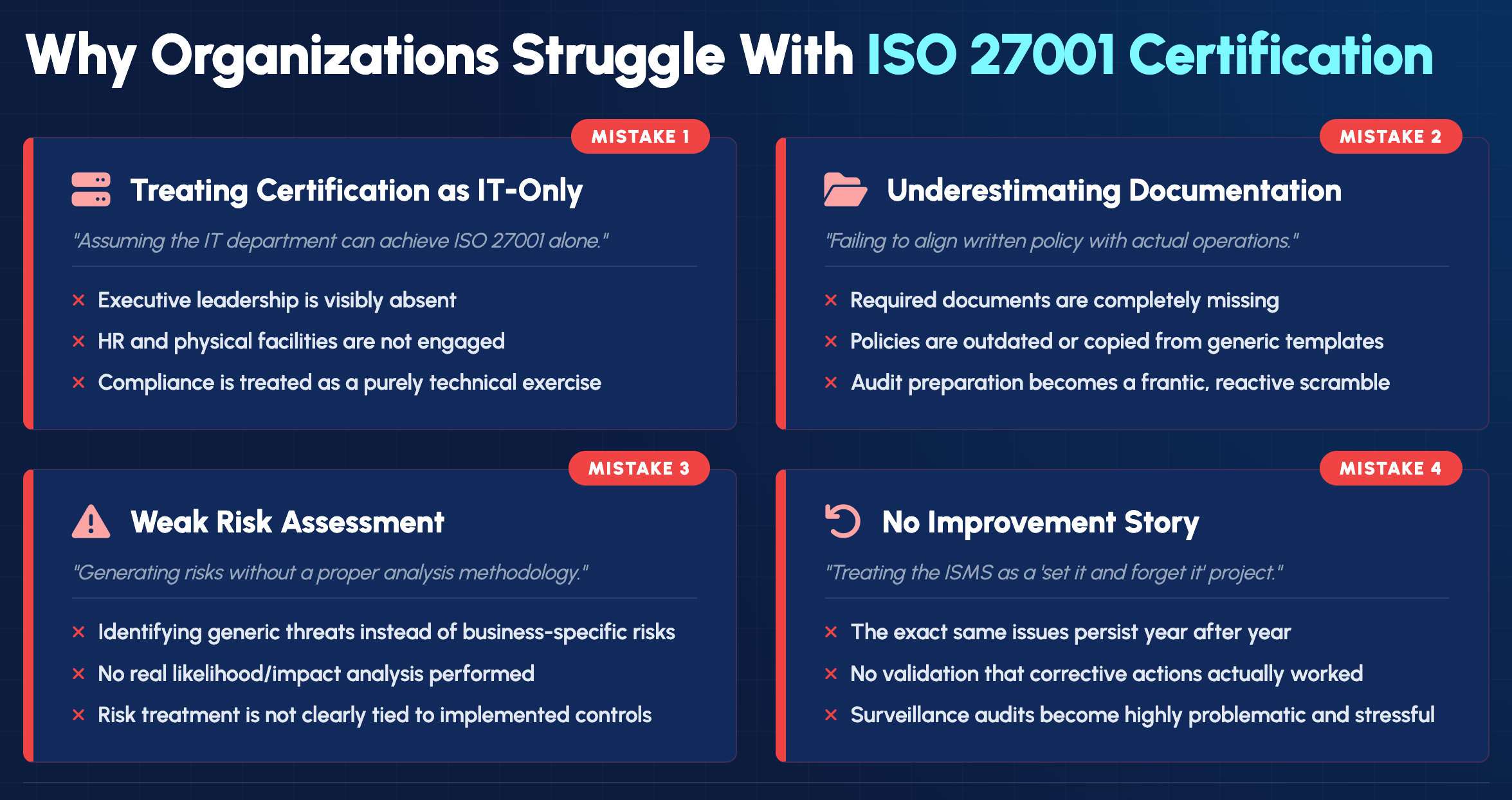
ISO 27001 explicitly requires organization-wide involvement. HR is responsible for people controls including screening, employment terms, and disciplinary processes. Legal and compliance teams must address regulatory requirements within the ISMS scope. Operations and facilities teams own physical security controls. Leadership must demonstrate active governance. Organizations that route the entire certification effort through the IT department consistently struggle with clauses related to leadership commitment, context of the organization, and human resource security. The ISMS must be institutionally owned, not technically owned.
ISO 27001 requires extensive documented information — not because auditors want paper, but because documentation is how organizations demonstrate that the ISMS is systematic and repeatable rather than ad hoc. Required documentation includes an information security policy, an ISMS scope definition, a risk assessment methodology and risk register, a risk treatment plan, a Statement of Applicability, monitoring and measurement results, evidence of competence and awareness, internal audit results, and management review records. Organizations that begin their certification effort without a documentation plan frequently find themselves in a documentation sprint in the weeks before their audit.
The risk assessment is the analytical core of the ISMS, and auditors evaluate it carefully. Superficial risk assessments that list generic threats without evaluating their specific applicability, probability, and impact rarely satisfy auditors. The methodology must be documented, consistently applied, and repeatable — different assessors using the same methodology should reach similar conclusions. Risk assessments that are completed once and never updated are also problematic; the standard requires reassessment when significant changes occur and at defined intervals.
Many organizations focus heavily on the initial certification audit and treat subsequent surveillance audits as maintenance tasks. Auditors in surveillance and recertification audits specifically look for evidence that the ISMS has improved since the last assessment — that nonconformities from previous audits have been addressed, that new risks have been identified and treated, and that the organization is actively refining its security practices rather than coasting on its initial certification. A static ISMS is a red flag.

Take the first step toward ISO 27001 certification today.
Comprehensive Support
Expert Guidance
Contact our team to schedule an initial consultation and discover how our tailored approach can help your organization achieve world-class information security management.
We use cookies to enhance site performance and user experience. Your data stays private — we don’t sell your information or share it with unrelated third parties. To find out more about the cookies we use, view our Privacy Policy.