The Gramm-Leach-Bliley Act requires financial institutions to protect customer information through written security programs, privacy notices, and controls against pretexting. The FTC’s 2023 amendments to the Safeguards Rule significantly expanded technical requirements—adding specific mandates for encryption, multi-factor authentication, penetration testing, and designated security personnel.
Non-compliance triggers enforcement actions, fines, and reputational damage. This guide covers what GLBA actually requires, which institutions must comply, the updated Safeguards Rule specifics, and practical steps for building a compliant information security program.
GLBA creates three categories of requirements for financial institutions: privacy obligations governing how you disclose customer information, security obligations requiring protection of that information, and pretexting prohibitions preventing fraudulent access to customer data.
The Privacy Rule governs how financial institutions collect, use, and share nonpublic personal information (NPI). NPI includes any personally identifiable financial information—account numbers, income, Social Security numbers, transaction history, and similar data.
Initial privacy notice. When a customer relationship begins, you must provide a clear, conspicuous notice describing what information you collect, how you use it, how you protect it, and with whom you share it.
Annual privacy notice. Customers must receive privacy notices annually throughout the relationship—though an exception exists if your practices haven’t changed and you only share information in ways that don’t require opt-out rights.
Opt-out rights. Before sharing NPI with nonaffiliated third parties (with certain exceptions), you must give customers the opportunity to opt out. The notice must explain how to exercise this right and provide a reasonable method to do so.
The Safeguards Rule requires financial institutions to develop, implement, and maintain a comprehensive information security program. The FTC significantly amended this rule in 2023, adding specific technical requirements that transformed it from a principles-based standard to a more prescriptive framework.
This rule drives most compliance effort and examination focus. The detailed requirements are covered in the next section.
GLBA prohibits obtaining customer information through false pretenses—impersonating customers, using forged documents, or other deceptive tactics. While this primarily targets bad actors attempting to access information fraudulently, institutions must implement safeguards to detect and prevent pretexting attempts.
This means verifying customer identity before disclosing information, training staff to recognize social engineering attempts, and establishing procedures for handling suspicious requests.
GLBA applies to “financial institutions”—a broader category than banks alone. The definition includes any company significantly engaged in financial activities.
Banks, credit unions, securities firms, and insurance companies obviously qualify. But GLBA’s reach extends further to mortgage lenders and brokers, payday lenders, finance companies, financial advisers and investment advisers, tax preparation firms, debt collectors, real estate settlement services, and entities providing wire transfer services.
If financial activities represent a significant portion of your business, GLBA likely applies. Auto dealers offering financing, retailers with credit card programs, and colleges administering financial aid may fall under GLBA requirements.
Different regulators enforce GLBA depending on institution type. The FTC covers non-bank financial institutions. The OCC, Federal Reserve, FDIC, and NCUA cover their respective depository institution types. State insurance commissioners cover insurance activities. SEC and CFTC cover securities and commodities firms.
The FTC’s Safeguards Rule applies to non-bank financial institutions. Banking regulators have issued similar but not identical guidelines for their supervised institutions.
The FTC’s 2023 amendments transformed the Safeguards Rule from general principles into specific mandates. Financial institutions under FTC jurisdiction must now meet detailed technical and operational requirements.
You must designate a Qualified Individual responsible for overseeing and implementing your information security program. This person can be an employee or outsourced—but if outsourced, a senior employee must still oversee the service provider.
The Qualified Individual must have appropriate knowledge and authority to implement the program effectively. They’re responsible for the annual written report to the board.
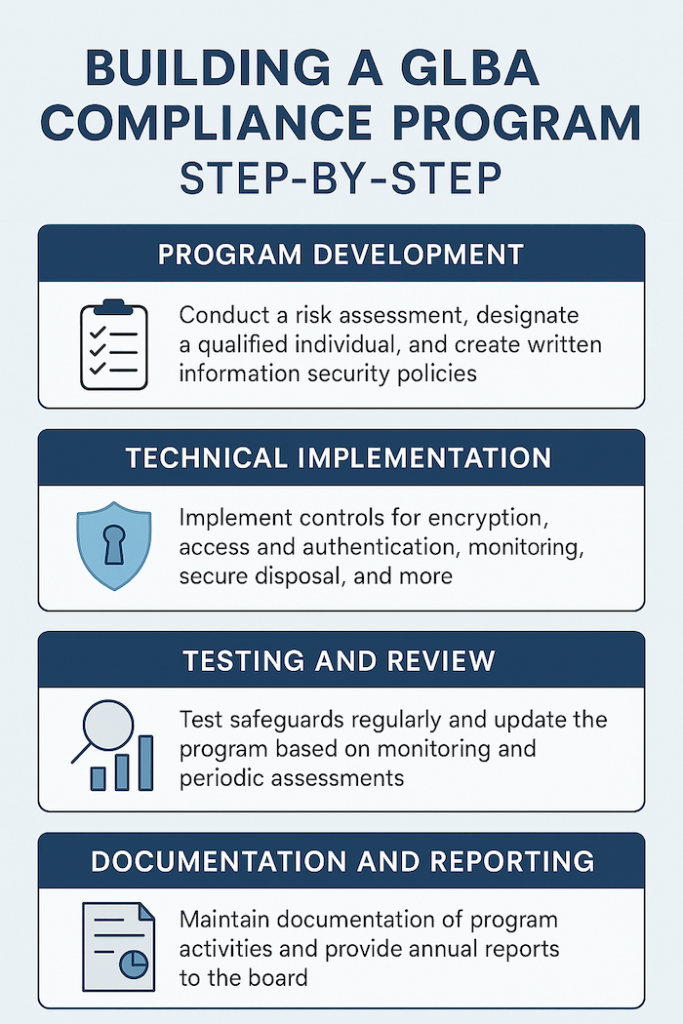
Your information security program must be based on a written risk assessment that identifies reasonably foreseeable internal and external risks to customer information, assesses the sufficiency of current safeguards, and documents how identified risks will be addressed.
The risk assessment must be written—verbal or informal assessments don’t satisfy the requirement. It must be updated periodically as risks evolve.
The 2023 rule mandates specific safeguards rather than leaving implementation entirely to institutional judgment.
Access controls. Implement and periodically review access controls to limit who can access customer information to authorized users with a legitimate business need.
Inventory of data and systems. Know what customer information you have and where it resides. You can’t protect what you don’t know exists.
Encryption. Encrypt customer information both in transit and at rest. If encryption isn’t feasible for data at rest, you must document why and implement alternative controls approved by the Qualified Individual.
Multi-factor authentication. Require MFA for anyone accessing customer information—or implement equivalent controls approved by the Qualified Individual in writing.
Secure development practices. If you develop applications, implement secure development practices. If you use third-party applications, evaluate and test their security.
Disposal procedures. Securely dispose of customer information no longer needed for business or legal purposes within two years of last use.
Change management. Implement procedures to evaluate, test, and approve changes to information systems that might affect security.
Monitoring. Implement policies and procedures to monitor authorized user activity and detect unauthorized access or tampering.
The rule requires regular testing of your safeguards.
Penetration testing. Conduct annual penetration testing of your information systems.
Vulnerability assessments. Conduct vulnerability assessments at least every six months—or continuous monitoring instead of periodic assessments.
These aren’t suggestions. Missing testing requirements creates clear compliance violations.
You must maintain a written incident response plan addressing goals, internal processes for responding to security events, clear roles and responsibilities, internal and external communications, remediation requirements, documentation procedures, and post-incident review processes.
The plan must be tested and updated as necessary.
When service providers access customer information, you must select providers capable of maintaining appropriate safeguards, contractually require them to implement safeguards, and periodically assess their continued adequacy.
Vendor management isn’t optional—it’s a specific regulatory requirement.
The Qualified Individual must provide written reports to the board of directors (or equivalent governing body) at least annually. Reports must address the overall status of the information security program and compliance with the Safeguards Rule, material matters related to the program including risk assessments, risk management decisions, service provider arrangements, testing results, security events, and management responses.
If you don’t have a board, the report goes to a senior officer responsible for the information security program.
Personnel must receive security awareness training. The training should address current threats and how employees can recognize and respond to them.
Financial institutions face technical requirements embedded throughout the Safeguards Rule—encryption, MFA, penetration testing, monitoring, and secure development practices. IT GOAT provides specialized support for organizations building compliant information security programs.
Risk assessments evaluate your current security posture against Safeguards Rule requirements, identifying gaps and prioritizing remediation.
Technical implementation deploys required controls including encryption, multi-factor authentication, access management, and monitoring systems.
Penetration testing and vulnerability assessments satisfy testing requirements with documented results and remediation tracking.
Financial institutions maintaining customer information for fewer than 5,000 consumers are exempt from certain requirements: the written risk assessment requirement, the incident response plan requirement, and the annual board reporting requirement.
The core safeguards requirements still apply. This exemption reduces documentation burden for smaller institutions but doesn’t eliminate security obligations.
Privacy notices must be clear, conspicuous, and accurate. Required content includes categories of NPI you collect, categories of NPI you disclose, categories of affiliates and nonaffiliates receiving NPI, policies for protecting former customers’ information, categories of information disclosed to service providers and joint marketers, and explanation of opt-out rights and methods.
Timing matters. Initial notices must be provided when the customer relationship is established. For loans, this means at closing. For other services, it’s when you begin providing services.
Delivery method. Notices can be provided in writing or electronically (with proper consent). Simply posting a notice on your website doesn’t satisfy delivery requirements for existing customers.
Recognized for excellence with numerous industry awards, reflecting our commitment to delivering top-tier IT solutions. Our accolades showcase our dedication to innovation, quality service, and client satisfaction.

If you’re a non-bank financial institution under FTC jurisdiction, the 2023 amendments apply. Banks and credit unions follow guidelines from their primary federal regulators, which are similar but not identical. Check with your regulator if jurisdiction is unclear.
GLBA doesn’t specify credentials. The person must have sufficient knowledge, skills, and authority to implement the program effectively. This could be an internal employee or an outsourced provider—but if outsourced, a senior internal employee must oversee them.
Yes, the rule doesn’t require rotating firms. However, using the same firm repeatedly may create blind spots. Consider periodic rotation or supplementing with different perspectives.
If encryption isn’t feasible for certain data at rest, document why and implement alternative compensating controls. The Qualified Individual must approve this in writing. This exception exists but shouldn’t become the default approach.
Maintaining customer information for fewer than 5,000 consumers exempts you from certain documentation requirements—not from implementing safeguards. Count customers whose information you actually maintain, not just current customers.
IT GOAT simplifies cybersecurity by integrating over 750+ enterprise apps to make sure your business runs smoothly.

The 2023 FTC Safeguards Rule requires financial institutions to protect customer information through specific controls, including:
These requirements apply to mortgage lenders, tax preparers, finance companies, debt collectors, auto dealers offering financing, and other financial institutions under FTC jurisdiction.
Civil penalties reach $100,000 per violation for institutions. Officers and directors face personal liability.
Partner with IT GOAT to implement the technical controls the Safeguards Rule requires.
We use cookies to enhance site performance and user experience. Your data stays private — we don’t sell your information or share it with unrelated third parties. To find out more about the cookies we use, view our Privacy Policy.