Defense contractors handling Controlled Unclassified Information face a specific compliance requirement that determines whether they can bid on DoD contracts: DFARS clause 252.204-7012. This regulation mandates cybersecurity controls based on NIST SP 800-171, requires incident reporting within 72 hours, and flows down to every subcontractor in your supply chain.
Getting DFARS wrong doesn’t just risk contract loss—it creates False Claims Act exposure and potential debarment. This guide covers what DFARS actually requires, how it connects to CMMC 2.0, and the practical steps to achieve and maintain compliance.
The Defense Federal Acquisition Regulation Supplement extends the Federal Acquisition Regulation with defense-specific requirements. For cybersecurity, the critical clause is 252.204-7012, “Safeguarding Covered Defense Information and Cyber Incident Reporting.”
This clause applies when your contract involves Covered Defense Information—essentially any CUI marked or identified in the contract, or CUI you generate in performance of the contract. If you’re a subcontractor and CUI flows to you, the requirement flows with it.
Implement NIST SP 800-171 controls. The 110 security controls across 14 families form the technical baseline. These cover access control, audit logging, incident response, system integrity, and related security domains. You must implement all applicable controls or document your plan to address gaps.
Report cyber incidents within 72 hours. Any incident affecting covered defense information triggers mandatory reporting to the DoD through the DIBNet portal. This includes providing malicious software samples, preserving images for 90 days, and supporting damage assessments.
Flow requirements to subcontractors. If subcontractors handle CUI, they face the same obligations. You’re responsible for ensuring flowdown language appears in subcontracts and that your supply chain maintains compliance.
DFARS clause 252.204-7012 establishes the requirement; CMMC provides the verification mechanism. Under the current framework:
The CMMC rollout means contractors who’ve been self-attesting will face external validation. Organizations that haven’t genuinely implemented controls—as opposed to just claiming compliance—face significant remediation timelines.
DFARS 252.204-7012 applies to contractors and subcontractors when contracts involve CUI. This typically includes:
The clause doesn’t apply to contracts for commercial off-the-shelf products without modification, but the boundaries get technical. When in doubt, assume compliance applies.
Cyber incident reporting catches many contractors off guard. Within 72 hours of discovering an incident affecting covered defense information, you must:
“Discovery” means when you reasonably should have known—not when you confirmed the full scope. This timeline demands incident response capabilities that can detect, assess, and report rapidly.

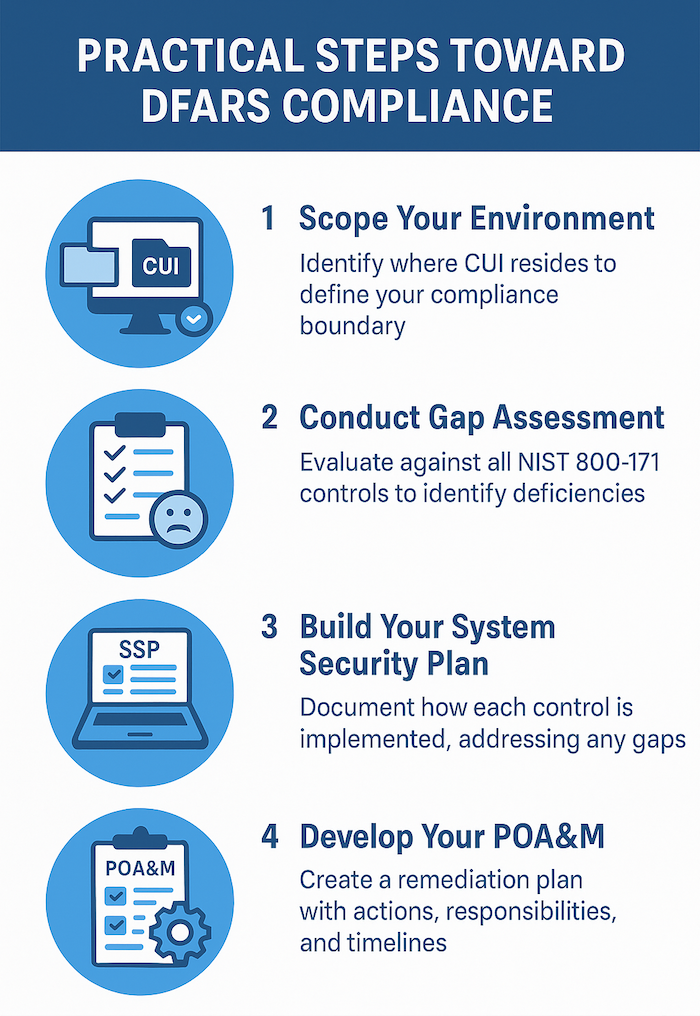
Identify where CUI lives in your organization—systems, applications, file shares, email, physical documents. The smaller your CUI boundary, the fewer systems require full NIST 800-171 implementation. Many contractors reduce compliance burden by segmenting CUI into dedicated enclaves rather than applying controls enterprise-wide.
Evaluate your current state against all 110 NIST 800-171 controls. Document which controls you’ve fully implemented, partially implemented, or haven’t addressed. This assessment becomes the foundation for your System Security Plan and POA&M.
The SSP documents how you implement each control—or how your POA&M addresses gaps. This isn’t a checkbox exercise; assessors review SSPs to understand your actual security posture. Generic template language without organization-specific detail raises red flags.
The Plan of Action and Milestones tracks controls you haven’t fully implemented. Each entry needs specific remediation steps, responsible parties, resource requirements, and completion dates. Under current DFARS, you can self-attest with a POA&M in place—but CMMC assessments will scrutinize whether POA&M items are genuine plans or indefinite deferrals.
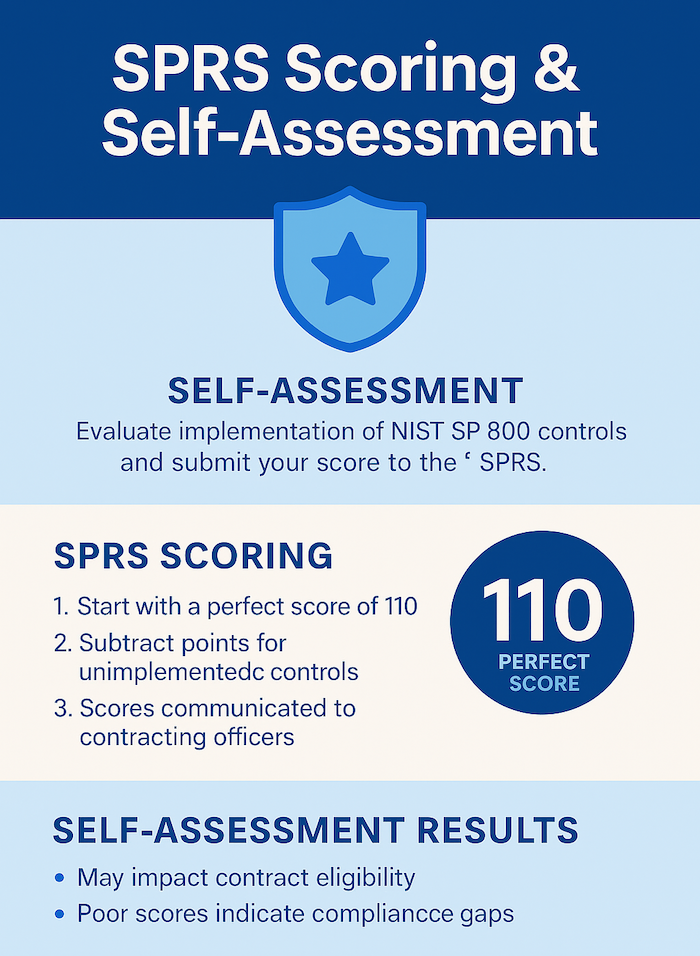
The Supplier Performance Risk System score reflects your self-assessed compliance level. A perfect score is 110; each unimplemented control reduces the score based on its weighted value. DoD contracting officers can see your score, and some solicitations specify minimum score requirements.
IT GOAT provides specialized support for organizations navigating DFARS and preparing for CMMC certification.
Gap assessments identify where your current controls fall short of NIST 800-171 requirements, with prioritized remediation roadmaps based on risk and resource constraints.
Technical implementation addresses control gaps across access management, audit logging, encryption, endpoint protection, and network segmentation.
Continuous monitoring maintains compliance between assessments, identifying configuration drift and emerging gaps before they become findings.
Assessment preparation ensures your organization is ready for CMMC third-party assessments with mock evaluations and evidence collection support.
Underestimating scope. Organizations often discover CUI in unexpected places—legacy file shares, email archives, backup systems, personal devices. Thorough scoping prevents compliance gaps that surface during assessments.
Confusing policy with implementation. Having a written policy doesn’t satisfy a control requirement. Assessors verify that technical controls actually function and that personnel follow documented procedures.
Ignoring supply chain flowdown. Your compliance posture includes your subcontractors. Failing to flow down requirements—or failing to verify subcontractor compliance—creates liability exposure.
Treating compliance as a project rather than a program. DFARS compliance requires continuous monitoring, regular assessments, and ongoing maintenance. Annual checkbox exercises don’t sustain the security posture the regulation demands.
Recognized for excellence with numerous industry awards, reflecting our commitment to delivering top-tier IT solutions. Our accolades showcase our dedication to innovation, quality service, and client satisfaction.

The clause applies when your DoD contract involves Covered Defense Information—CUI that’s marked, designated, or generated during contract performance. If CUI touches your systems or your subcontractors’ systems, compliance applies. Contracts for purely commercial items without CUI involvement typically don’t trigger the requirement.
DFARS establishes the compliance requirement; CMMC creates the certification framework. Currently, DFARS allows self-attestation of NIST 800-171 compliance. As CMMC rolls out, certain contracts will require third-party certification at Level 2 or Level 3, verifying that contractors actually implement the controls they’ve claimed.
You must still report within 72 hours regardless of compliance status. However, operating with known compliance gaps while self-attesting creates False Claims Act exposure. The combination of an incident plus demonstrated non-compliance significantly increases legal and contractual risk.
Under current DFARS, a POA&M allows you to acknowledge gaps while maintaining eligibility. However, POA&M items should represent genuine remediation plans with realistic timelines—not permanent deferrals. CMMC assessments will evaluate whether POA&M items reflect active remediation or compliance avoidance.
IT GOAT simplifies cybersecurity by integrating over 750+ enterprise apps to make sure your business runs smoothly.
DFARS clause 252.204-7012 establishes cybersecurity requirements for defense contractors handling Controlled Unclassified Information, including:
These requirements apply when DoD contracts involve CUI, technical data, or controlled specifications—including subcontract flowdown from primes.
Non-compliance means False Claims Act exposure, potential debarment, and lost contract eligibility as CMMC requirements roll out.
Work with IT GOAT to assess your posture and build a compliance roadmap.
We use cookies to enhance site performance and user experience. Your data stays private — we don’t sell your information or share it with unrelated third parties. To find out more about the cookies we use, view our Privacy Policy.