A cyberattack on your email server might leak sensitive data. A cyberattack on your factory’s control system could injure workers or shut down production for weeks. That fundamental difference, protecting information versus protecting physical operations and human safety—sits at the heart of IT versus OT security.
This guide breaks down what separates these two security disciplines, where they overlap, and why the growing convergence between IT and OT networks creates both opportunity and risk for modern businesses.

Cyberattacks targeting operational technology are no longer rare and their impact is significantly more severe than traditional IT incidents. According to IBM and industry reports, ransomware attacks on industrial organizations can result in average downtime costs exceeding $100,000 per hour, depending on the operation.
Recent incidents highlight the real-world consequences:
Unlike IT breaches, which primarily impact data, OT attacks directly affect physical operations, revenue, and human safety, making them a top priority for modern cybersecurity strategies.
Information Technology (IT) security focuses on protecting data confidentiality and integrity across corporate networks, while Operational Technology (OT) security prioritizes the safety, availability, and reliability of physical industrial systems. IT manages information flow, whereas OT controls physical machinery—making OT breaches potential safety hazards that can cause real-world harm beyond data loss.
Operational technology refers to the hardware and software that monitors and controls physical processes in industrial environments. Think of the systems running a manufacturing plant, a power grid, or a water treatment facility. Unlike IT systems that handle emails and spreadsheets, OT systems interact directly with the physical world—opening valves, controlling temperatures, and moving machinery.
The most common OT systems include:
Information technology security protects the data, networks, servers, and applications that keep businesses running day to day. The foundation of IT security rests on the CIA triad—confidentiality, integrity, and availability—prioritized in that order. Keeping sensitive data private comes first, followed by ensuring data accuracy, then maintaining system access.
Typical IT assets include workstations, cloud platforms, databases, email servers, and business applications. IT teams patch and update systems frequently, often replacing hardware every three to five years as technology evolves.

Both disciplines aim to protect critical assets, yet their approaches differ dramatically based on what they’re protecting and why. The table below highlights the core distinctions.
| Factor | IT Security | OT Security |
|---|---|---|
| Primary goal | Data confidentiality | System availability and safety |
| Environment | Office and cloud networks | Industrial and manufacturing floors |
| Device lifecycle | 3-5 years typical | 15-30 years common |
| Patching frequency | Weekly or monthly | Annually or less |
| Downtime tolerance | Hours acceptable | Minutes can be catastrophic |
IT security follows the CIA triad with confidentiality at the top. OT security flips this to AIC—availability first, then integrity, then confidentiality. The reasoning is straightforward: a brief OT outage at a power plant affects thousands of customers, while a manufacturing line stoppage costs thousands of dollars per minute.
Industry estimates show:
The difference in downtime tolerance between IT and OT environments is measurable in financial terms. While IT outages can be disruptive, OT downtime often results in immediate revenue loss and operational risk.
IT systems operate in climate-controlled offices with stable power and network connectivity. OT systems function in harsh conditions—extreme temperatures, vibration, dust, and humidity. This environmental difference limits which security tools can actually be deployed in OT settings, since many standard IT security products simply won’t survive on a factory floor.
OT networks were historically “air-gapped,” meaning completely isolated from other networks and the internet. IT networks are built for connectivity and data sharing by design. This fundamental architectural difference shapes how security teams approach each environment, though the gap between them is shrinking rapidly.
IT systems receive patches weekly or monthly, and teams replace hardware regularly. OT systems often run for decades without updates because patching typically requires a complete production shutdown. Some industrial controllers still run Windows XP—not from negligence, but because the cost and risk of upgrading outweighs the security benefits when the system controls a critical process.
Legacy infrastructure is one of the defining challenges of OT security. According to industry research:
These systems were designed for reliability and longevity—not cybersecurity. As a result, many lack:
This creates a persistent risk that cannot be solved through patching alone, requiring compensating controls like segmentation and monitoring.
IT security frameworks like SOC 2, ISO 27001, and HIPAA focus on data protection. OT environments face industry-specific regulations emphasizing operational resilience—NERC CIP for energy, IEC 62443 for industrial automation, and various safety standards depending on the sector.
When IT detects a threat, teams can often isolate or shut down compromised systems to contain the damage. OT incident response looks completely different. You can’t simply turn off a water treatment plant or power grid. OT teams work to maintain operations while addressing threats, which requires specialized skills and pre-planned response procedures that account for physical safety.
Despite their differences, IT and OT security share common ground. Both face sophisticated attackers, including ransomware groups and nation-state actors who increasingly target industrial systems. The threat landscape has converged significantly as attackers who once focused exclusively on stealing data now target OT systems, knowing that operational disruption creates urgency to pay ransoms.
Core security practices apply to both environments:
Threat actors are increasingly targeting OT environments as organizations connect industrial systems to broader networks. According to Fortinet and other cybersecurity reports:
This shift reflects a change in attacker strategy. Moving from data theft to operational disruption, where the pressure to restore services often leads to faster ransom payments.
IT/OT convergence describes the integration of previously isolated operational technology systems with corporate IT networks and the internet. This trend has accelerated as organizations seek operational benefits like remote monitoring, predictive maintenance, and real-time analytics.
Plant managers want dashboards showing production metrics. Maintenance teams want predictive alerts before equipment fails. Executives want data-driven insights into operational efficiency. All of this requires connecting OT systems to IT infrastructure, which brings both opportunity and risk.
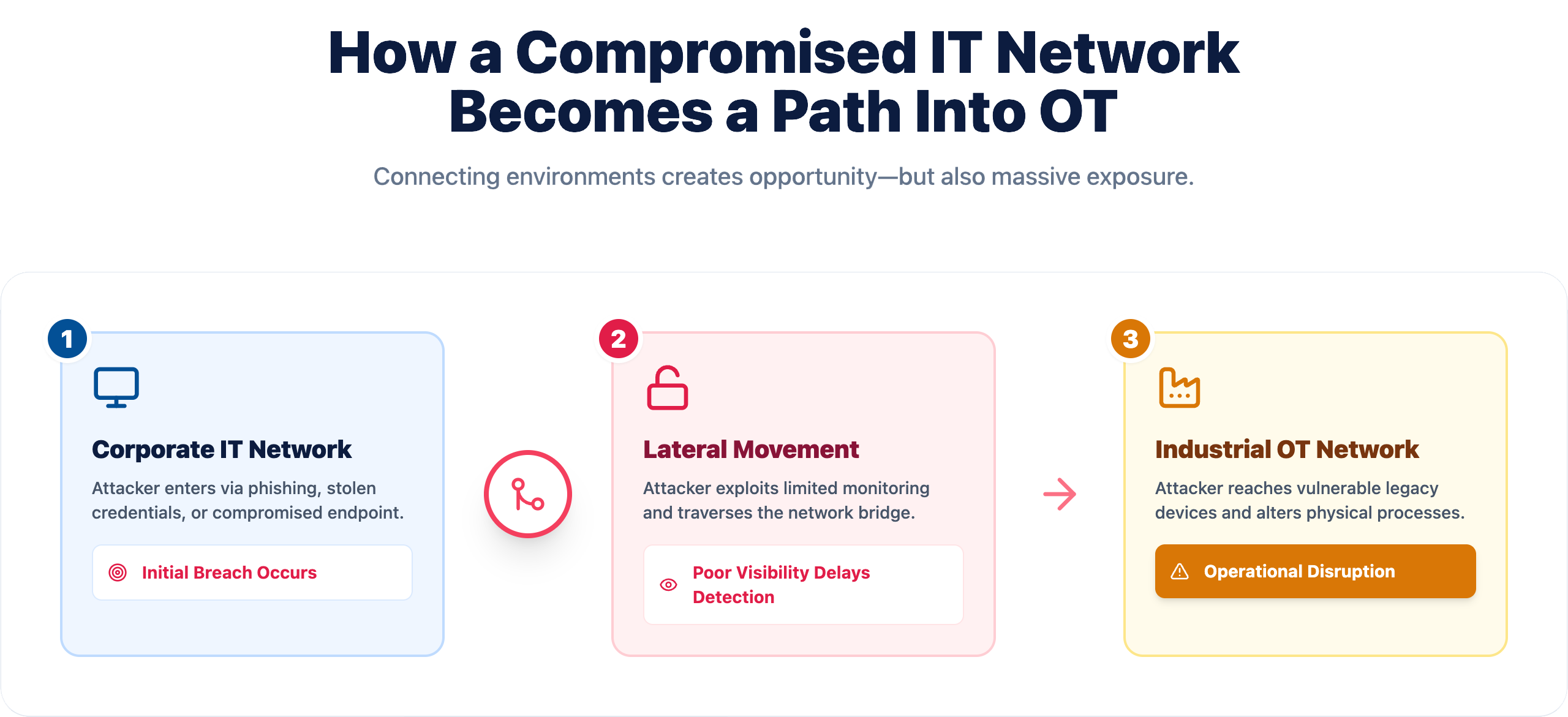
Connecting OT to IT networks creates new attack pathways that didn’t exist when systems were isolated. Attackers can now potentially reach critical industrial controls through compromised IT systems, expanding the attack surface significantly.
One of the most critical risks in converged environments is lateral movement from IT systems into OT networks. Industry analysis shows that a large percentage of OT breaches originate in IT environments first.
Key findings include:

This highlights why IT and OT security can no longer operate independently. Without proper segmentation and coordinated defenses, the IT network effectively becomes a gateway into critical industrial systems.
Many OT devices predate modern cybersecurity entirely. They were designed for reliability and longevity, not security. These systems often can’t run antivirus software, lack encryption capabilities, and may operate on obsolete operating systems that no longer receive security updates from vendors.
Without proper boundaries between IT and OT environments, a breach in one area can spread to the other. Attackers frequently use compromised IT systems as stepping stones to reach industrial controls. Proper segmentation creates barriers that slow or stop lateral movement between network zones.
Traditional IT security tools don’t understand industrial protocols like Modbus, DNP3, or BACnet. This creates blind spots where malicious activity can go undetected. Organizations often discover they have far less visibility into OT traffic than they assumed once they start looking closely.
OT environments commonly suffer from security basics that IT teams addressed years ago—factory-default passwords never changed, credentials shared across entire shifts, and minimal use of multi-factor authentication. These weaknesses become critical vulnerabilities once systems connect to broader networks.
Understanding specific vulnerabilities helps organizations prioritize remediation efforts and allocate security resources effectively.

End-of-life software running critical processes represents a significant risk. When vendors stop providing security updates, known vulnerabilities remain exploitable indefinitely. Organizations often face difficult choices between operational continuity and security improvements.
Vendor-set passwords that never get changed remain surprisingly common in industrial environments. Shared credentials eliminate individual accountability and make it impossible to track who accessed what systems and when—a problem during both security incidents and compliance audits.
Remote access for vendors and maintenance teams often gets installed without proper security review. These connections frequently lack strong authentication, logging, or monitoring—creating convenient entry points for attackers who know where to look.
Many OT environments lack adequate logging and alerting for industrial network traffic. Security intrusions can persist for months before detection, giving attackers ample time to understand systems and plan their attacks.
Bridging the traditional divide between IT and OT departments creates stronger security outcomes than either team can achieve alone. This collaboration requires intentional effort, as these groups often have different priorities, vocabularies, and organizational cultures.
Coordinated approaches close gaps that exist between domains. When IT and OT teams share threat intelligence and expertise, they achieve more comprehensive coverage than siloed efforts allow.
Shared tools, unified policies, and combined expertise reduce redundant work and eliminate confusion. Organizations often discover they’ve been duplicating efforts or leaving gaps because teams weren’t communicating effectively.
Collaboration enables consolidated security investments and reduces incident remediation costs. Preventing a single major incident typically justifies years of collaborative security investment.
When threats span both environments, joint response teams act more quickly and decisively. Eliminating handoffs between separate teams reduces response time during critical incidents when minutes matter.

Organizations can begin integrating their security approaches through a structured, phased process that builds capability over time.
Start by identifying every IT and OT asset connected to your network, including hardware, software, and the connections between them. Many organizations discover unknown devices during this process—equipment that’s been running for years without anyone tracking it.
Create distinct network zones separating OT from corporate IT. Use firewalls and strict access policies to control traffic between zones. This limits the blast radius if either environment gets compromised.
Deploy security tools capable of understanding both IT and OT protocols. The goal is a single view across both environments, enabling security teams to detect threats regardless of where they originate.
Create governance frameworks addressing both IT and OT requirements. Involve stakeholders from both teams in policy development to ensure practical, implementable standards that work in real-world conditions.
Working with a managed service provider that understands both IT and OT security accelerates capability building. Look for partners offering proactive monitoring, rapid incident response, and deep industrial knowledge.

Managing converged IT/OT environments requires specialized expertise that many organizations lack internally. A trusted security partner provides the proactive monitoring, rapid incident response, and strategic guidance necessary to protect critical operations without building everything in-house.
For businesses seeking unified IT and OT security support, book a consultation with IT GOAT to discuss your environment and security goals.
Manufacturing, energy utilities, water treatment, healthcare facilities, and transportation all benefit from integrated IT and OT security protection—essentially any industry where technology controls physical processes.
Yes, experienced managed service providers with OT expertise deliver unified security monitoring, incident response, and strategic guidance across both environments—often more cost-effectively than building internal capabilities from scratch.
Implementation timelines vary based on organization size, system complexity, and existing infrastructure. Most organizations benefit from a phased approach spanning months to years rather than attempting full integration all at once.
Begin with comprehensive asset discovery to identify all connected devices, followed by risk assessment to understand vulnerabilities and prioritize remediation based on potential business impact.
Small businesses can partner with managed security providers specializing in both IT and OT environments, gaining access to expertise and monitoring capabilities without hiring specialized internal staff.
See the power of IT GOAT.
The world’s most advanced cybersecurity platform catered specifically to your business’ needs.
Keep up to date with our digest of trends & articles.
By subscribing, I agree to the use of my personal data in accordance with IT GOAT Privacy Policy. IT GOAT will not sell, trade, lease, or rent your personal data to third parties.

Mitigate All Types of Cyber Threats
Experience the full capabilities of our advanced cybersecurity platform through a scheduled demonstration. Discover how it can effectively protect your organization from cyber threats.

IT GOAT: Threat Intel & Cyber Analysis
We are experts in the field of cybersecurity, specializing in the identification and mitigation of advanced persistent threats, malware, and exploit development across all platforms.

Protect Your Business & Operations
Exceptional performance in the latest evaluations, achieving 100% prevention rate and providing comprehensive analytic coverage, unmatched visibility, and near-instant detection of threats.
We use cookies to enhance site performance and user experience. Your data stays private — we don’t sell your information or share it with unrelated third parties. To find out more about the cookies we use, view our Privacy Policy.