HITRUST certification demonstrates that your organization meets a defined set of security controls validated by an independent assessor. Unlike self-attestation frameworks, HITRUST requires third-party verification—making it a common requirement for healthcare vendors, business associates, and organizations handling sensitive data.
The framework consolidates requirements from HIPAA, NIST, ISO 27001, PCI DSS, and other standards into a single assessment. This guide covers the three certification types, what assessments actually evaluate, realistic timelines and costs, and practical steps for achieving certification.
HITRUST (Health Information Trust Alliance) created the HITRUST CSF (Common Security Framework)—a certifiable security framework that maps controls from multiple regulations and standards. Organizations undergo assessments against CSF requirements, and successful completion results in certification.
Customer requirements. Healthcare organizations increasingly require HITRUST certification from vendors and business associates. It’s becoming table stakes for selling into healthcare.
Regulatory coverage. A single HITRUST assessment addresses controls from HIPAA, HITECH, NIST 800-53, ISO 27001, PCI DSS, and state privacy laws. This reduces the burden of multiple compliance efforts.
Third-party validation. Unlike HIPAA (which has no certification mechanism), HITRUST provides independent verification that controls are implemented—not just documented.
Risk management. The framework forces systematic evaluation of security controls, often identifying gaps that internal assessments miss.
HITRUST is most common in healthcare and adjacent industries: healthcare providers and health systems, health plans and payers, healthcare clearinghouses, business associates handling PHI, health IT vendors and SaaS providers, and life sciences and pharmaceutical companies.
Increasingly, organizations outside healthcare pursue HITRUST when customers require it or when they want consolidated compliance across multiple frameworks.
HITRUST offers three assessment types with different rigor, cost, and assurance levels. Choosing the right one depends on customer requirements, risk profile, and resources.
The entry-level assessment covers 44 controls addressing fundamental cybersecurity practices. It’s designed for lower-risk organizations or those beginning their HITRUST journey.
Scope: Essential cybersecurity hygiene—basic access controls, malware protection, incident response fundamentals.
Validation: Self-assessment with assessor verification of a sample of controls.
Validity: 1 year.
Best for: Organizations with lower risk profiles, those new to HITRUST, or situations where customers accept e1 certification.
Limitation: Many healthcare organizations require i1 or r2—e1 may not satisfy contractual requirements.
The mid-tier assessment covers approximately 182 controls representing a more comprehensive security program. It provides moderate assurance with less effort than r2.
Scope: Broader security program including threat management, access control, risk management, and third-party assurance.
Validation: Assessor validates implementation of all controls (not just a sample).
Validity: 1 year.
Best for: Organizations needing more than e1 but not ready for full r2 rigor, or where customers accept i1 certification.
Note: i1 assessments use a static control set—the same 182 controls regardless of organization size or complexity.
The comprehensive assessment tailors control requirements based on organizational risk factors. Control counts vary but typically range from 350-500+ depending on scope.
Scope: Full security program assessment with controls tailored based on risk factors including organization size, data types, regulatory requirements, and system characteristics.
Validation: Assessor validates implementation and operational effectiveness of all applicable controls.
Validity: 2 years, with an interim assessment at the 1-year mark.
Best for: Organizations where customers require r2, those handling high-risk data, or organizations wanting the most comprehensive validation.
Industry standard: r2 certification is what most healthcare organizations mean when they require “HITRUST certification.”
HITRUST uses a maturity-based scoring model. Each control receives a score from 0-100 based on implementation maturity across five levels:
Policy (15 points): Documented policies exist addressing the control requirement.
Procedure (20 points): Documented procedures implement the policy.
Implemented (25 points): Evidence demonstrates the control operates as documented.
Measured (20 points): Metrics track control effectiveness.
Managed (20 points): Control performance is actively managed and improved.
To pass, controls must score at least 62 (generally requiring Policy + Procedure + Implemented). The overall assessment must meet minimum thresholds across all controls.
Controls scoring below 62 require Corrective Action Plans (CAPs). You can still achieve certification with CAPs in place if the overall assessment meets requirements and CAPs demonstrate a credible remediation path.
However, too many CAPs or CAPs on critical controls can prevent certification. Address known gaps before assessment rather than relying on CAPs.
HITRUST’s value proposition includes mapping to multiple frameworks, potentially reducing duplicate compliance efforts.
HITRUST CSF incorporates HIPAA Security Rule requirements. A HITRUST certification doesn’t equal HIPAA compliance (HIPAA has no certification), but it demonstrates you’ve implemented controls addressing HIPAA requirements.
Many covered entities accept HITRUST certification as evidence of business associate security practices.
HITRUST offers a combined SOC 2 + HITRUST assessment option. A single engagement produces both a SOC 2 report and HITRUST certification, reducing assessment fatigue and cost compared to separate assessments.
The SOC 2 report uses HITRUST CSF as the control framework rather than generic Trust Services Criteria.
HITRUST CSF maps to NIST 800-53 and NIST Cybersecurity Framework controls. Organizations with NIST requirements can demonstrate alignment through HITRUST certification.
For organizations using cloud infrastructure or SaaS platforms, HITRUST supports control inheritance. If your cloud provider has HITRUST certification, you may inherit certain controls rather than implementing them yourself.
This requires the provider to participate in HITRUST’s inheritance program and provide inheritance documentation. Major cloud providers (AWS, Azure, Google Cloud) offer HITRUST inheritance for applicable controls.
Understanding shared responsibility is critical—you’re still responsible for controls the provider doesn’t cover.
HITRUST certification demands security expertise, project management discipline, and sustained effort. IT GOAT provides comprehensive support for organizations pursuing certification.
Readiness assessments evaluate your current security posture against HITRUST requirements, identifying gaps and estimating remediation effort.
Remediation support addresses control gaps through policy development, technical implementation, and process improvement—preparing your environment for successful assessment.
Ongoing compliance support maintains controls between assessments, preparing for interim assessments and recertification.
HITRUST certification requires significant investment. Understanding realistic expectations prevents surprises.
e1 Assessment: 3-6 months from kickoff to certification, assuming reasonable security maturity.
i1 Assessment: 6-9 months for organizations with existing security programs. Longer if significant gaps exist.
r2 Assessment: 9-18 months depending on scope, existing maturity, and remediation needs. First-time r2 assessments typically take 12+ months.
These timelines assume dedicated resources. Organizations treating HITRUST as a side project extend timelines significantly.
MyCSF subscription: Annual fee based on assessment type and organizational factors. Typically $15,000-$40,000+ annually.
Assessor fees: External assessor engagement for validation. Ranges from $30,000-$50,000 for e1/i1 to $80,000-$150,000+ for r2 depending on scope and complexity.
Remediation costs: Addressing control gaps often exceeds assessment costs. Budget for technology implementations, policy development, and process changes.
Internal resources: Staff time for evidence collection, control documentation, and assessor coordination. Plan for significant time commitment from security, IT, and compliance personnel.
Total investment: First-time r2 certification commonly costs $150,000-$400,000+ including all components. Subsequent certifications cost less as controls mature.
Recognized for excellence with numerous industry awards, reflecting our commitment to delivering top-tier IT solutions. Our accolades showcase our dedication to innovation, quality service, and client satisfaction.

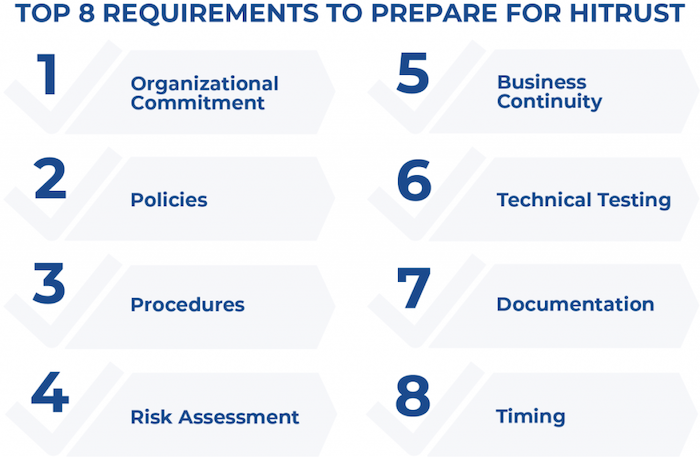
Effective preparation determines whether you achieve certification on schedule or face delays and additional costs.
Before committing to formal assessment, conduct a readiness assessment (gap analysis) against HITRUST requirements. This identifies control gaps, estimates remediation effort, and informs realistic timelines.
Readiness assessments can be internal or conducted by consultants. Many assessor firms offer readiness services separate from formal assessment.
Define your assessment scope carefully. HITRUST assesses systems, applications, and processes within scope—broader scope means more controls and higher costs.
Consider scoping to specific systems handling sensitive data rather than your entire environment. Document scope clearly and ensure it satisfies customer requirements.
HITRUST requires evidence demonstrating control implementation. Start collecting evidence early—screenshots, configuration exports, policy documents, training records, and logs supporting each control.
Organize evidence by control requirement. Missing or inadequate evidence is a common assessment delay.
Controls require documented policies and procedures. Generic templates rarely satisfy HITRUST requirements—documentation must reflect your actual operations.
Review existing documentation against HITRUST control requirements. Update or create policies addressing gaps.
Address identified gaps before formal assessment begins. Implementing controls during assessment creates timeline pressure and increases failure risk.
Prioritize remediation based on control criticality and scoring impact. Focus on achieving minimum maturity levels (Policy + Procedure + Implemented) across all applicable controls.
Timeline depends on assessment type and current maturity. e1 assessments take 3-6 months, i1 assessments 6-9 months, and r2 assessments 9-18 months. First-time r2 certifications typically require 12+ months. These assume dedicated resources and reasonable existing security maturity.
Total costs vary significantly based on assessment type, scope, and remediation needs. First-time r2 certifications commonly cost $150,000-$400,000+ including MyCSF subscription, assessor fees, remediation, and internal resources. Subsequent certifications cost less as controls mature.
Check customer and contractual requirements—many healthcare organizations specifically require r2 certification. If requirements don’t specify, consider your risk profile and resources. e1 provides basic validation, i1 offers moderate assurance, and r2 provides comprehensive validation that satisfies most requirements.
Not directly—SOC 2 and HITRUST are separate frameworks. However, HITRUST offers combined SOC 2 + HITRUST assessments that produce both deliverables from a single engagement. Existing SOC 2 controls likely overlap with HITRUST requirements, reducing remediation effort.
If your cloud providers have HITRUST certification and participate in the inheritance program, certain controls may be inherited rather than implemented by you. You’re still responsible for controls the provider doesn’t cover and must document the shared responsibility model.
You can remediate issues and continue the assessment. Corrective Action Plans address controls below minimum scores. However, significant gaps may require remediation before achieving certification. Thorough readiness assessment before formal assessment minimizes failure risk.
IT GOAT simplifies cybersecurity by integrating over 750+ enterprise apps to make sure your business runs smoothly.
HITRUST certification provides independently verified security controls—a common requirement for healthcare vendors and business associates, including:
These requirements apply when healthcare customers require certification, BAAs specify HITRUST, or organizations want consolidated compliance across HIPAA, NIST, and ISO frameworks.
First-time r2 certification costs $150,000-$400,000+ with 9-18 month timelines. Limited assessor capacity means scheduling delays.
Let IT GOAT guide your HITRUST journey from readiness through certification.
We use cookies to enhance site performance and user experience. Your data stays private — we don’t sell your information or share it with unrelated third parties. To find out more about the cookies we use, view our Privacy Policy.